Task1
What does the acronym SQL stand for?
问SQL的全称是什么
SQL的全称是 Structured Query Language
Task2
What is one of the most common type of SQL vulnerabilities?
问最常见的SQL漏洞是什么?
是SQL注入SQL injection
Task3
What is the 2021 OWASP Top 10 classification for this vulnerability?
问 OWASP top10列表对注入漏洞的命名为什么?
命名为A03:2021-Injection
Task4
What does Nmap report as the service and version that are running on port 80 of the target?
问80端口上运行的服务和版本是什么
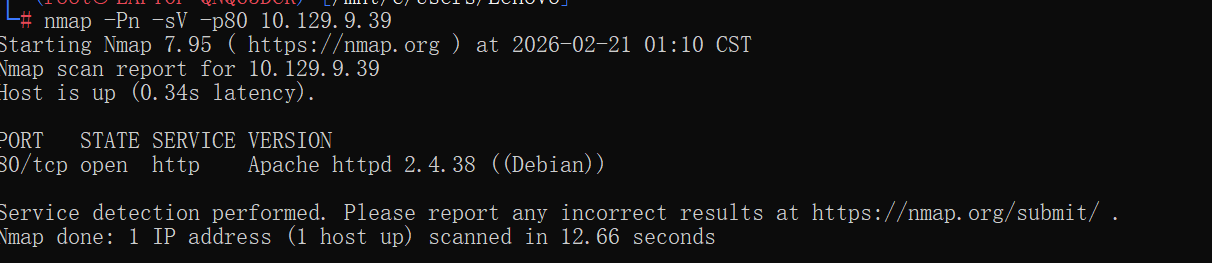
根据扫描结果直接写
Apache httpd 2.4.38 ((Debian))
Task5
What is the standard port used for the HTTPS protocol?
问https协议的标准端口是什么
常识,是443
Task6
What is a folder called in web-application terminology?
问在web术语里面,文件夹叫什么
directory
Task7
What is the HTTP response code is given for 'Not Found' errors?
HTTP协议中未找到的错误码是什么?
还是常识,404
Task8
Gobuster is one tool used to brute force directories on a webserver. What switch do we use with Gobuster to specify we're looking to discover directories, and not subdomains?
我们使用gobuster命令加上什么参数来表示 我们正在寻找的是目录,而不是子域?
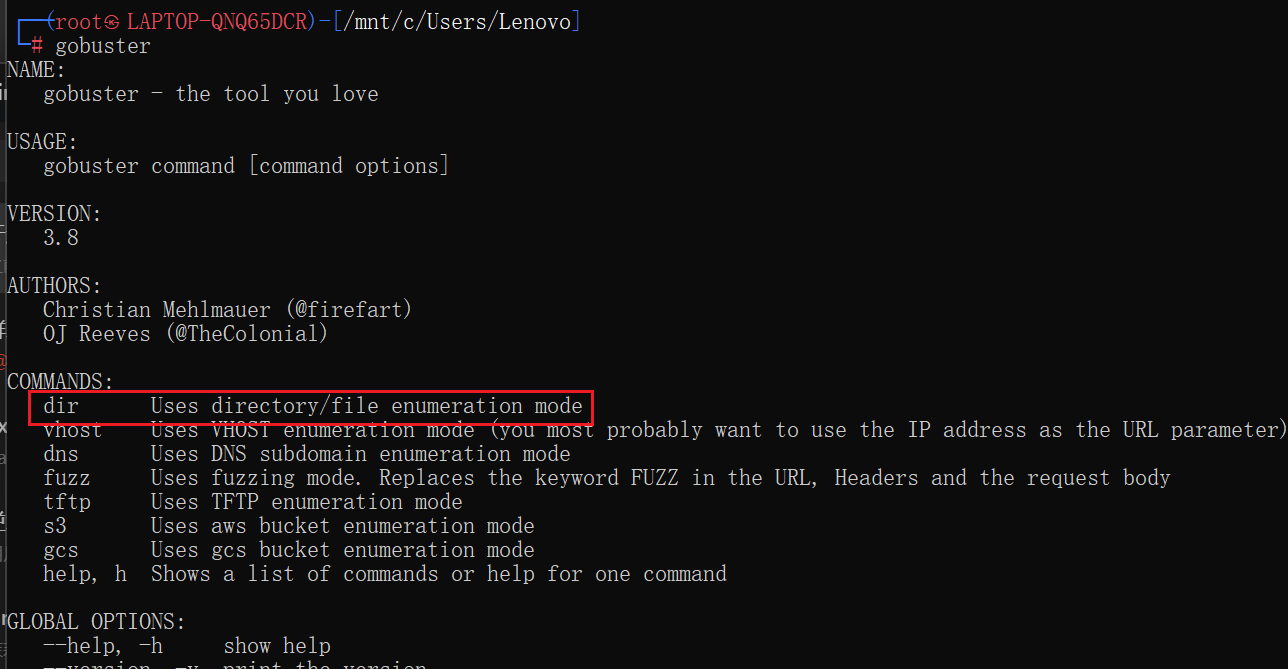
gobuster的参数dir是表示目录
dir
Task9
What single character can be used to comment out the rest of a line in MySQL?
问用什么符号来注释SQL代码,用#
Task10
If user input is not handled carefully, it could be interpreted as a comment. Use a comment to login as admin without knowing the password. What is the first word on the webpage returned?
问以admin身份登陆后网页返回的第一个单词是什么,这里开始要渗透靶机了,由于存在SQL注入漏洞且用户名指定为admin,所以直接用SQL注入漏洞登入
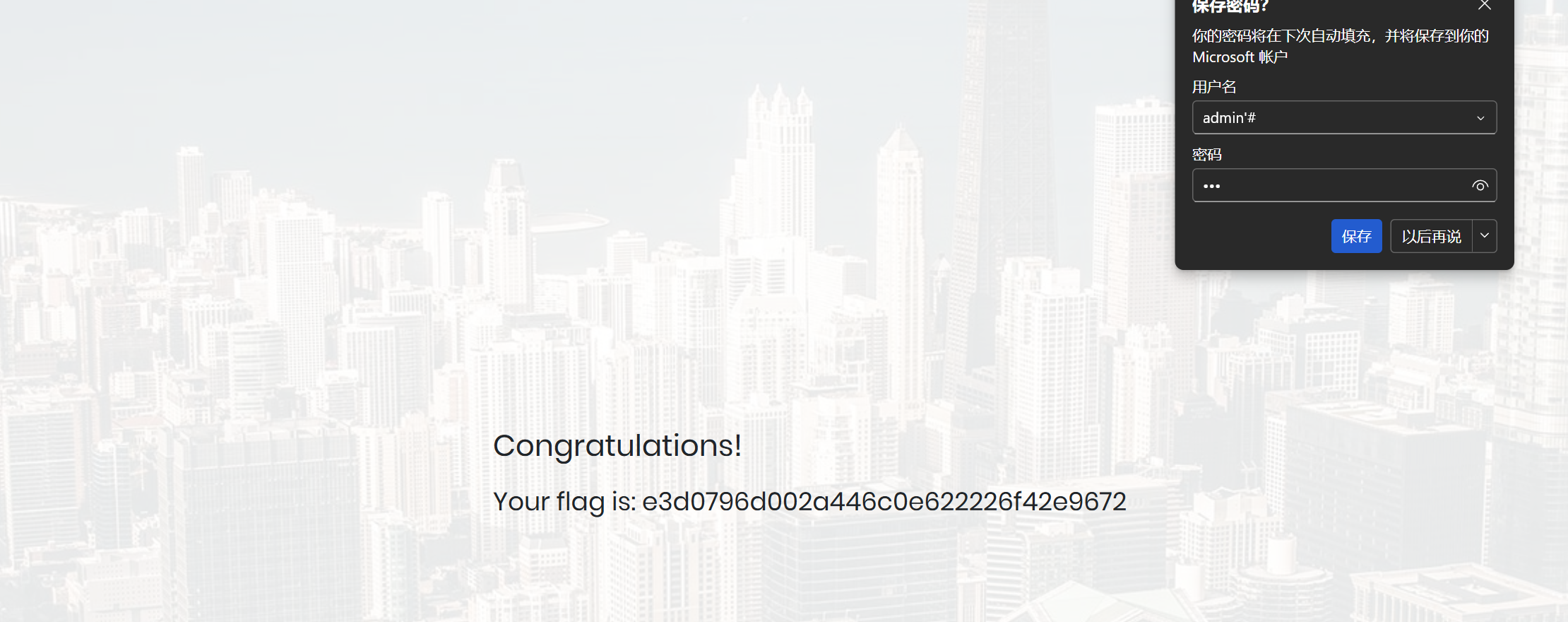
用户名写
1 | admin'# |
闭合原SQL语句的单引号,后面注释符注释后面的内容,密码随便填,就能成功登入了,这里看到单词是
Congratulations,flag也紧随其后
总结
SQL注入在渗透测试中是非常重要的一环,可以反复练习,这个靶机算比较基础的了